Cybersecurity Awareness Month is officially coming to an end—but that doesn’t mean implementing cybersecurity best practices should come to an end. Cyberattacks are rampant all year round.
To help keep you cyber safe today, and every day, we interviewed Checkmarx security experts to get their take on hot topics such as how to create strong passwords, the importance of two-step authentication, preventing phishing attacks, and maturing your application security (AppSec) programs.
Create Strong Passwords
Pete Chesna, CISO of North America, stressed the importance of strong passwords to prevent cyber criminals from accessing your accounts, whether personal or professional. Passwords should not only be hard to guess but also different for every cyber account.
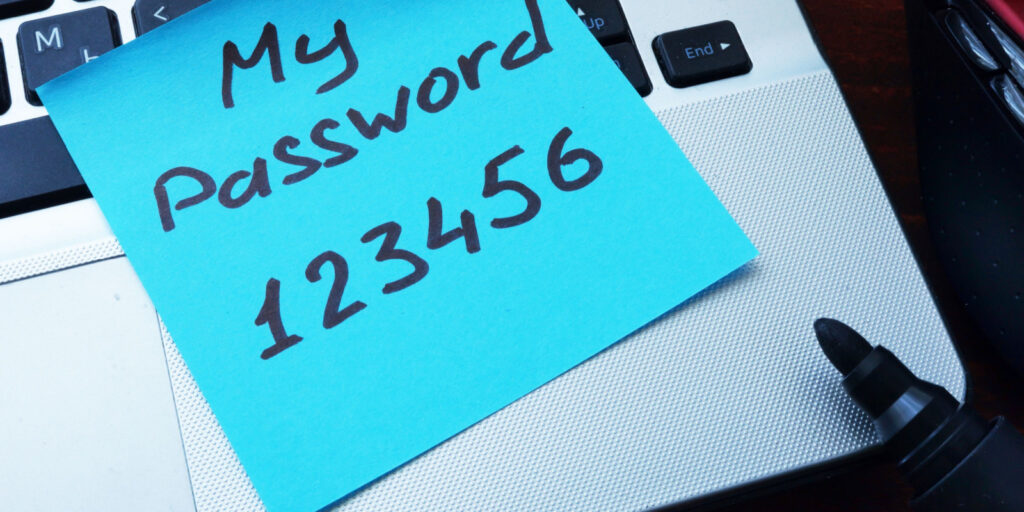
You might be thinking, “How am I supposed to remember a dozen different passwords for all of my accounts?” A lot of us are guilty of using an easy-to-remember password across all of our accounts so we are not staring at our browser for hours on end trying to remember the obscure string of letters, numbers, and symbols we used for various accounts. But if you use the same password for multiple accounts, a hacker now has access to all of those accounts.
Pete suggests you leverage a virtual password vault, which autogenerates strong passwords that can be securely stored and used on your desktop, mobile device, or tablet. With a virtual password vault, you can skip the tiresome memorization or messy (and risky) use of sticky notes.
Leverage Multi-Factor Authentication
Daniela da Cruz, Vice President of Engineering, suggests you also use multi-factor authentication (MFA) whenever possible. MFA is a way to ensure that even if one of your account credentials is successfully hacked, like your password, the cybercriminal still needs information from one of the other factors such as access to your smartphone, email, fingerprint, etc., to view your information.
Yes, leveraging MFA is a bit more time-consuming, but it’s critical when dealing with sensitive information. For example, anything to do with banking information or proprietary data should be protected by multi-factor authentication.
Don’t Fall Victim to Phishing Attacks
One common way that attackers steal login credentials is through phishing attacks. Bhawani Singh, Principal Solutions Architect, discussed how easy it is to get “hooked” by a phishing scam. Phishing scams have become very sophisticated. From hyper-personalized subject lines to tailored email addresses that appear to be coming from a reputable source, it’s no wonder IBM reported that in the past year, phishing attacks were the second largest cause of breaches.
To stay safe, it really comes down to behavioral changes. Take more time to review subject lines and sender addresses before opening emails; don’t click on suspicious links; and, when in doubt, always report potentially fraudulent emails. Organizations should also consider running simulated phishing campaigns to prepare employees for actual attacks.
Mature Your AppSec Program
As an application security company, we would be remiss if we didn’t mention ways to mature your application security program to better protect your software from potential breaches. Steve Boone, Head of Product Management, stressed the importance of leveraging multiple different types of testing tools to scan for vulnerabilities from code through production. He also stressed the importance of modernizing your application security program to reflect modern development practices. In other words, you need to make sure you are securing your containers, APIs, and infrastructure.
Investing in multiple testing types can be costly and time-consuming—especially if you leverage several different vendors. But it doesn’t have to be. Consider moving to a cloud-based AppSec platform like Checkmarx One™. Cloud-based platforms are more cost-effective and low maintenance. With Checkmarx One, you can trigger multiple scan engines with just one click. And with Checkmarx Fusion, you can see correlated scan results, allowing you to prioritize the most critical vulnerabilities first.
Explore More Ways to Stay Cyber Safe
We are here to help. Request a demo to learn how our products can keep your applications, and organization, secure.