Financial Services: DevSecOps Engineering
Software Composition Analysis
Checkmarx
Software
Composition Analysis
Identify, prioritize, and remediate open source risk in your applications, including vulnerabilities, malicious code, and license risks





















Everything You Need To
Mitigate Open Source Risk
Checkmarx provides extensive coverage and accurate results
across the core SCA software functions
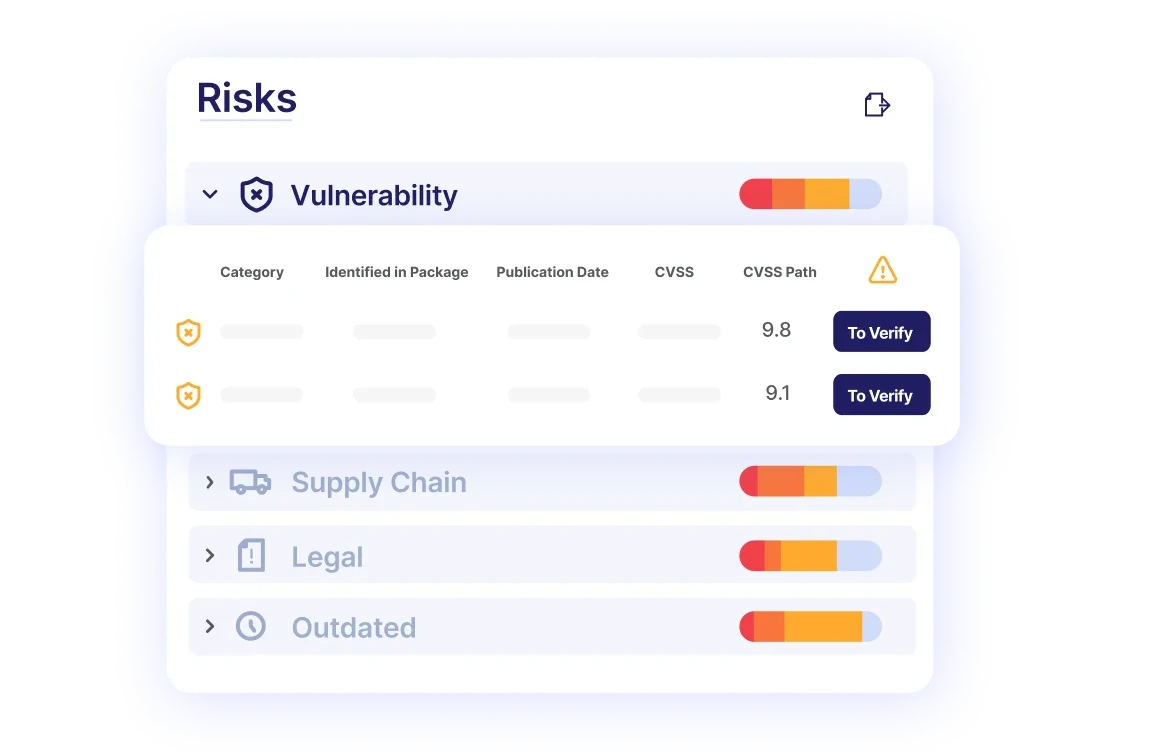
Software vulnerability detection
Identify vulnerabilities and license risks in your open source libraries, based on our analysis of >1M packages a month. Then easily address them with actionable remediation guidance.

Exploitable Path
Prioritize remediation in open source libraries by identifying vulnerable methods that are called by your code, and exploitable in your applications, to reduce the noise by
up to 70%.
Malicious package detection
Prevent malicious code from open source repositories from getting into your application. Checkmarx has identified more than 200,000 malicious packages to date
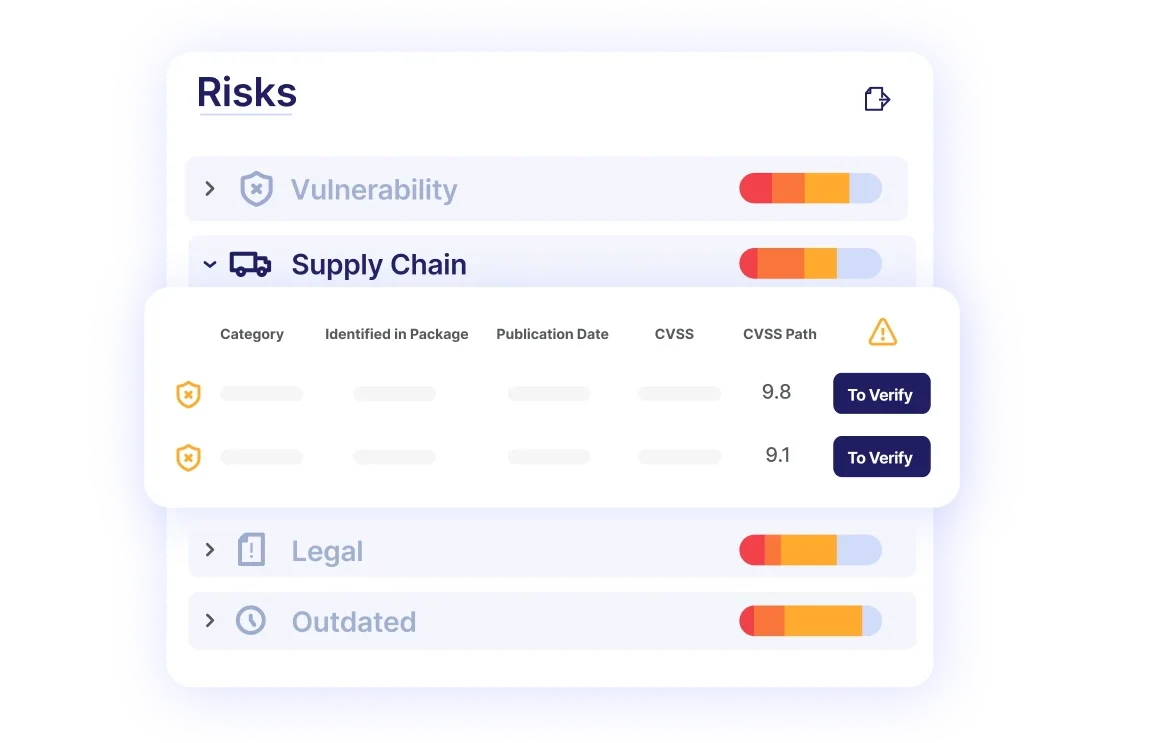
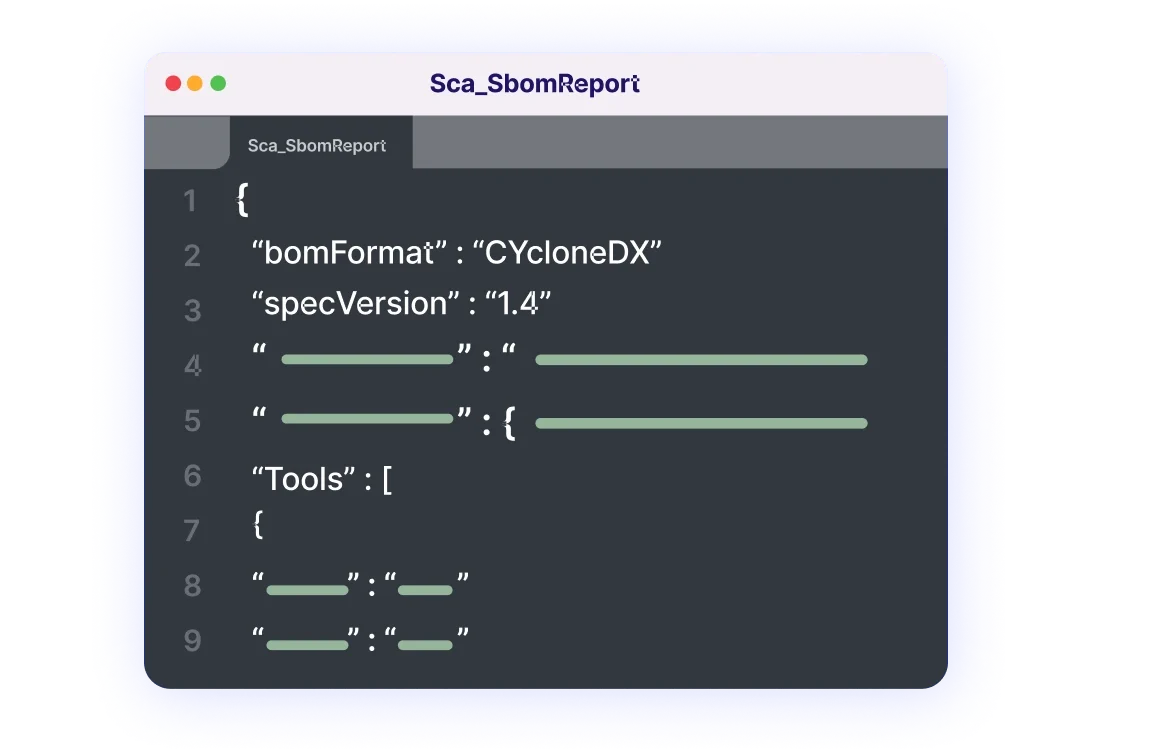
Software Bill Of Materials (SBOM)
Easily build an SBOM for your projects to inventory all the software components in your applications and understand your open source risk.
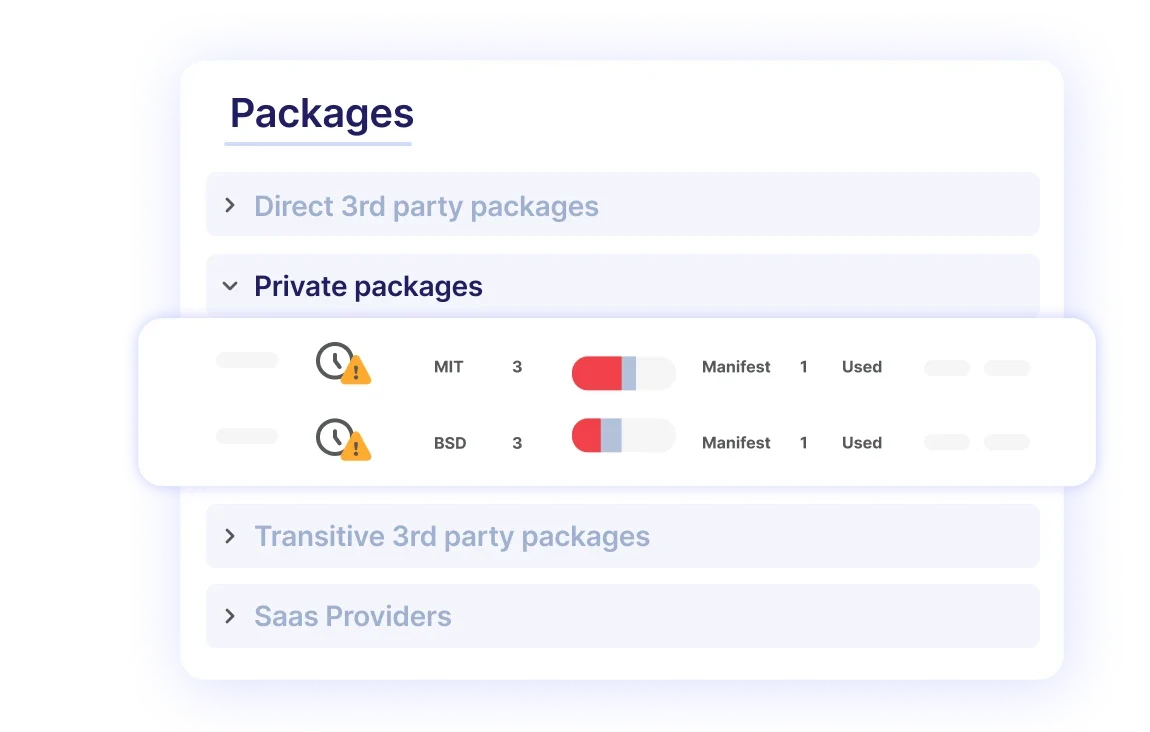
Private package scanning
Scan and analyze private packages in artifactories and internal registries for deeper insights into dependencies and potential risks.
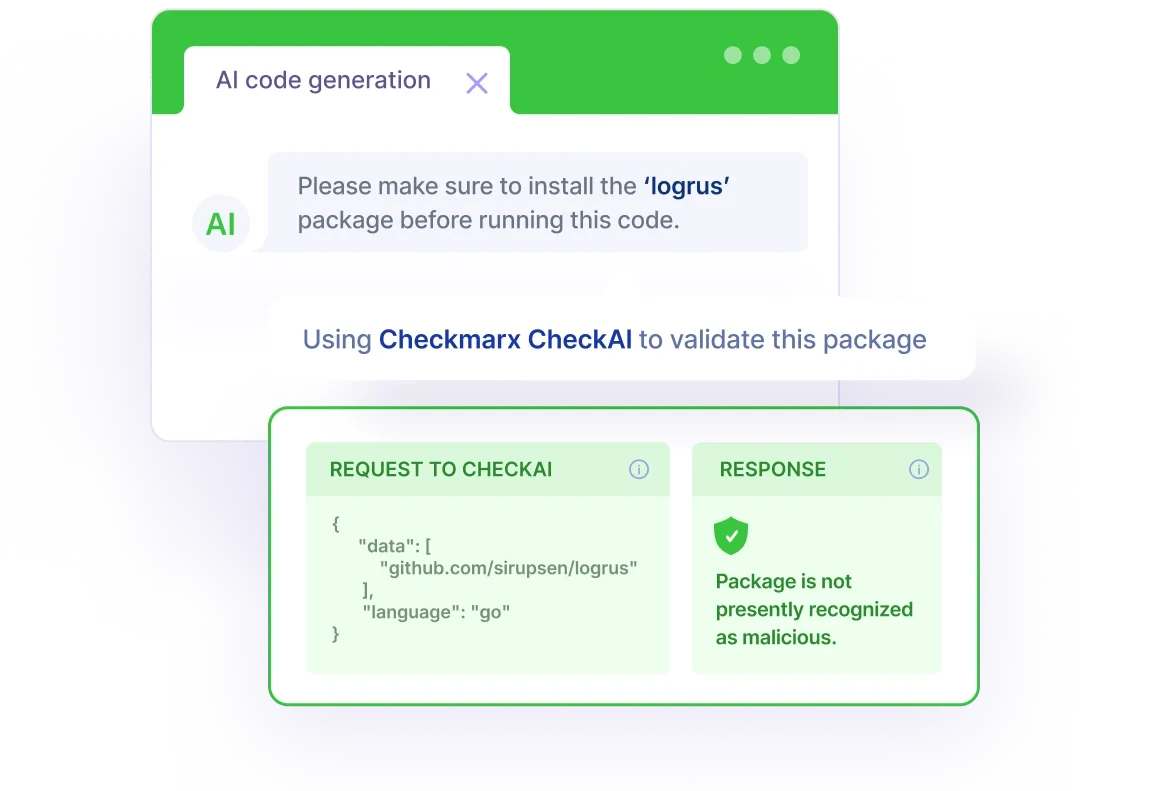
AI-Generated Code Scanning
Protect against attacks caused by malicious open source packages and dependencies, while working within popular AI code generation tools such as ChatGPT.
The Checkmarx One Approach To SCA
Better understand how to measure, manage, and remediate open source risk as an integrated part of your software development process.
How Organizations Benefit
from Checkmarx One SCA
SCA on Checkmarx One provides a one-stop solution for CISO, AppSec, and Devs
Minimize
open source risk
Confidently utilize open source software to launch new features and applications faster, with automated scans that don’t interrupt your developers’ workflow.
Better prioritize
remediation
Leverage correlated insights to reduce noise, focus on vulnerabilities that are actually exploitable to save your AppSec team and developers’ time and energy.
Build
#DevSecTrust
Developers can create secure applications faster with integrated application security in their existing tools and workflows.
Mitigate API Risk Faster
Discover and assess APIs everywhere – throughout the lifecycle, in documentation, source code, and dynamic testing – to address risks efficiently.
Prioritized Remediation
Focus your AppSec teams and developers on the most critical issues, by prioritizing API vulnerabilities based on their business value and risk.
What Our Customers Say
Customers who chose Checkmarx over others
“Checkmarx One definitely checks all my boxes from a security standpoint and has a great interface that’s engaging and easy to use. Some of the solutions we considered were more complicated. With Checkmarx One, it’s easy to get right to the problem with little to no learning curve.”
Cybersecurity and Networking Manager
The Forrester WaveTM: Software Composition Analysis, Q2 2023
"After reviewing the Checkmarx platform, I’m not sure how Veracode is able to exist while being at a similar price point."

Cybersecurity and Networking Manager
“Incorporating Checkmarx's technology has revolutionized our development culture. It's more than just technology; it serves as the foundation of our security strategy, ensuring that our applications are secure by design.”

Sr. Director, Product Security Engineering

The Forrester WaveTM: Software Composition Analysis, Q2 2023
“The success of our AppSec program can be directly attributed to the tooling, processes and support provided by Checkmarx managed services. Our mission revolves around providing secure and compliant lottery and gaming applications and services to our clients around the globe, and with Checkmarx SAST, SCA and associated components enhanced by their stellar service support, we deliver on this promise with confidence and certainty.”

Head of Information Security

The Forrester WaveTM: Software Composition Analysis, Q2 2023
“After nearly nine years of using Checkmarx's SAST, CGI's journey has been one of seamless integration and consistent satisfaction. The last three years have been particularly smooth, reflecting the solution's reliability and our successful partnership.”

Lead Security Analyst

The Forrester WaveTM: Software Composition Analysis, Q2 2023
"Checkmarx’s execution is impressive; it’s brought all the products under one cloud platform"

Cybersecurity and Networking Manager
The Forrester WaveTM: Software Composition Analysis, Q2 2023
"By Far The Best AppSec Tooling Decision We Have Made!!"

Cybersecurity and Networking Manager
The Forrester WaveTM: Software Composition Analysis, Q2 2023
"We were thrilled to find Checkmarx, which helped us improve the SLA for identifying and remediating risk, reduce risk and the number of vulnerabilities, and eliminate high- and meduim-risk issues."
Tech Lead, Red Team/DevSecOps
The Forrester WaveTM: Software Composition Analysis, Q2 2023
"Checkmarx made security team and developers life easier."

IT Services
The Forrester WaveTM: Software Composition Analysis, Q2 2023
Frequently Asked Questions
Static application security testing (SAST) scans proprietary code written by your developers for security vulnerabilities. Software composition analysis (SCA) scans open source libraries and 3rd-party components for security vulnerabilities, license risks, and other types of risks.
Because modern applications comprise proprietary code, open source libraries, and 3rd-party components, application security programs typically utilize both SAST and SCA to provide more insights to the codebase, and ensure the quality and security of the software.
A software bill of materials (SBOM) is a file that lists all the components within an application, including open source and 3rd-party components.
SBOMs help organizations see the makeup of an application to understand, assess, and address the security risk across all of its underlying components.
Checkmarx SCA can be easily integrated as part of your CI/CD pipeline, seamlessly working with a wide variety of CI/CD tools, including Jenkins, Azure DevOps, GitHub Actions, TeamCity, Bamboo.
Checkmarx SCA also integrates with all the most popular IDEs, including Visual Studio, VS Code, JetBrains, and Eclipse.
Checkmarx SCA is available as part of the Checkmarx One platform. Developers can also get it through a free plugin within JetBrains IntelliJ IDEA Ultimate and Visual Studio Code.
Find More Malicious Packages
Than Anyone Else
Take advantage of the Checkmarx Supply Chain Threat Intelligence API for the best coverage of the most malicious packages – both included within SCA or as a separately available API.
What CISOs say about Checkmarx
Customers who chose Checkmarx over others

PCL Construction

PCL Construction

PCL Construction
“With Checkmarx One, it’s easy to get right to the problem with little to no learning curve”

Joel Godbout
Manager, Cybersecurity and Networking | CISSP
Checkmarx One: The Enterprise Cloud-Native Application Security Platform
Checkmarx One delivers a full suite of enterprise AppSec solutions in a unified, cloud-based platform that allows enterprises to secure their applications from the first line of code to deployment in the cloud.
Get everything your enterprise needs to integrate AppSec across every stage of the SDLC and build a successful AppSec program.
FUSION
Correlate multi-engine scans automatically to prioritize finding and fixing business-critical vulnerabilities
ENGINES
Get started With Checkmarx SCA today
Join the growing club of enterprises that rely on Checkmarx SCA to secure open source and reduce license risk
Related Resources

White paper
A Guide to Modern API Security
Understand the challenges in securing your API footprint
White paper
The Checkmarx Approach to API Security
See how a shift-left approach to API security can help you secure shadow and zombie APIs

Ebook
The Ultimate Guide to Software Composition Analysis
Simplify, scale, and secure your enterprise with #DevSecTrust.

Solution Brief
Checkmarx Software Composition Analysis
Learn how the Checkmarx Security Champion Program empowers CISOs and AppSec leadership to create a security-first culture.

Report
Report: Leader in Gartner® 2022 Magic Quadrant™ for Application Security Testing
Learn how to get developer buy-in with stronger AppSec solution onboarding.


