
What Happened?
- Joint research of Checkmarx and Illustria resulted with an anomaly discovered in the open-source ecosystem
- Over 144,000 packages were published to NuGet, NPM, and PyPi by the same threat actors
- Investigation revealed a new attack vector – attackers spam open-source ecosystem with packages containing links to phishing campaigns
- All packages and related user accounts were most likely created using automation
- The packages share similar project description and auto-generated names
- The threat actors refer to retail websites with referral ids to benefit the threat actors with referral rewards
- Our teams disclosed the findings in this report and most of the packages were unlisted
Working Together, Keeping the Ecosystem Safe
The ongoing battle against software supply chain attackers continues to be challenging as attackers constantly adapt and surprise with new techniques. In order to better defend against these threats, Checkmarx and Illustria have joined forces and combined their research efforts. This collaboration led to the discovery of a significant anomaly in the NuGet, NPM, and PyPi ecosystems.
NuGet Anomalies
Our technology collects and indexes evidence related to packages from all open-source ecosystems, allowing us to query historical data for new insights and discover suspicious activities through a process we call “retro-hunting.”
A few months ago, we discovered an anomaly in the NuGet ecosystem when we cross-referenced new information with our databases. Clusters of packages had been published in large quantities to the NuGet package manager. Further investigation revealed that the packages were part of a new attack vector, with attackers spamming the open-source ecosystem with packages containing links to phishing campaigns.
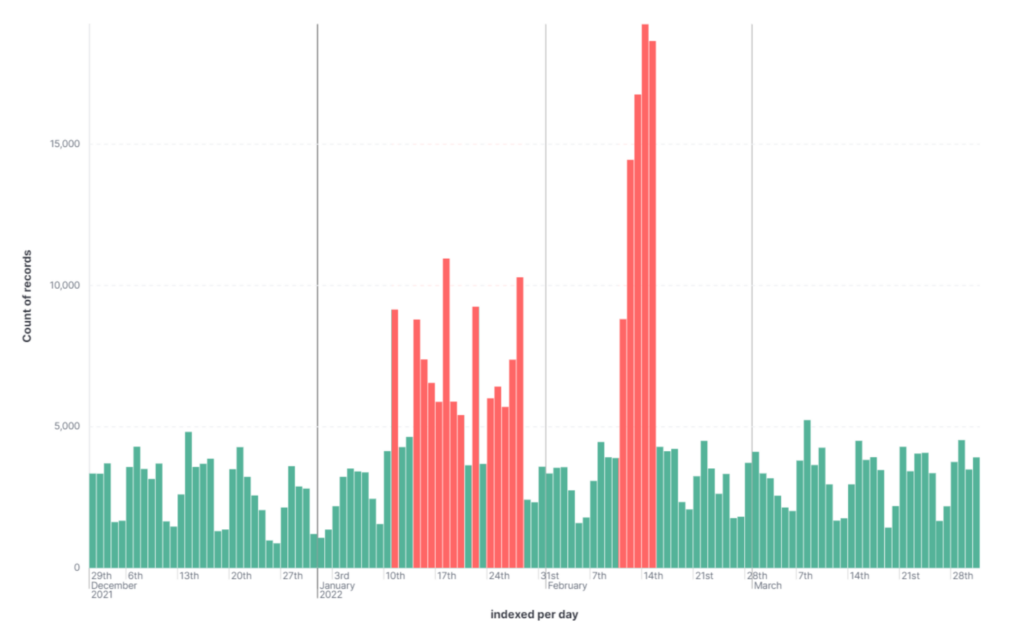
In this situation, it seems that automated processes were used to create over 135,000 packages in NuGet and related user accounts. The descriptions for these packages contained links to phishing campaigns. Our teams alerted the NuGet security team, and they replied that the packages were unlisted to protect users of the open-source ecosystem.
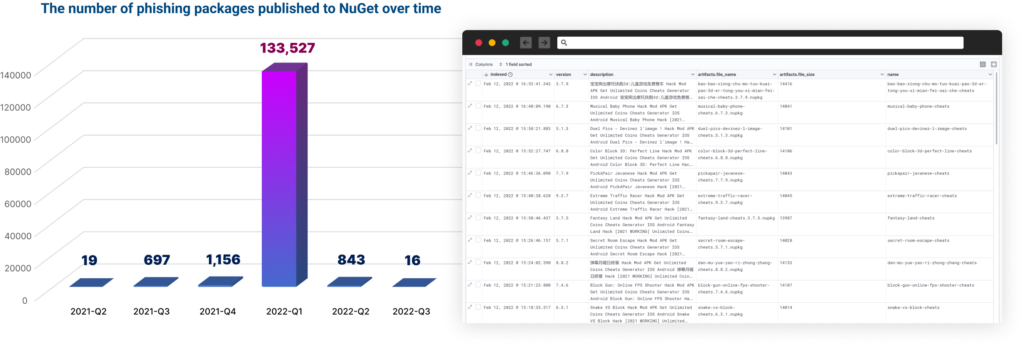
After investigating the NuGet anomaly with the creation of over 135,000 packages and related user accounts, we discovered that similar activity had also taken place in NPM and PyPi.
A total of 144,294 phishing-related packages were detected, all of which were created by the same threat actor. Of these, 136,258 were published on NuGet, 212 on NPM, and 7,824 on PyPi
Automated Packages and User Accounts
The large scale of the NuGet package publication and the patterns in the user accounts suggest that the process was automated. Many of the usernames followed the pattern “<a-z><1900-2022>”, and many users had published the same number of packages. Our team disclosed this information to the NuGet security team, who unlisted the packages from NuGet’s search results. While the packages are no longer easily accessible, their web pages are still available on NuGet’s website, and the packages can still be downloaded from these pages. Regarding the other ecosystems, the packages were taken down.
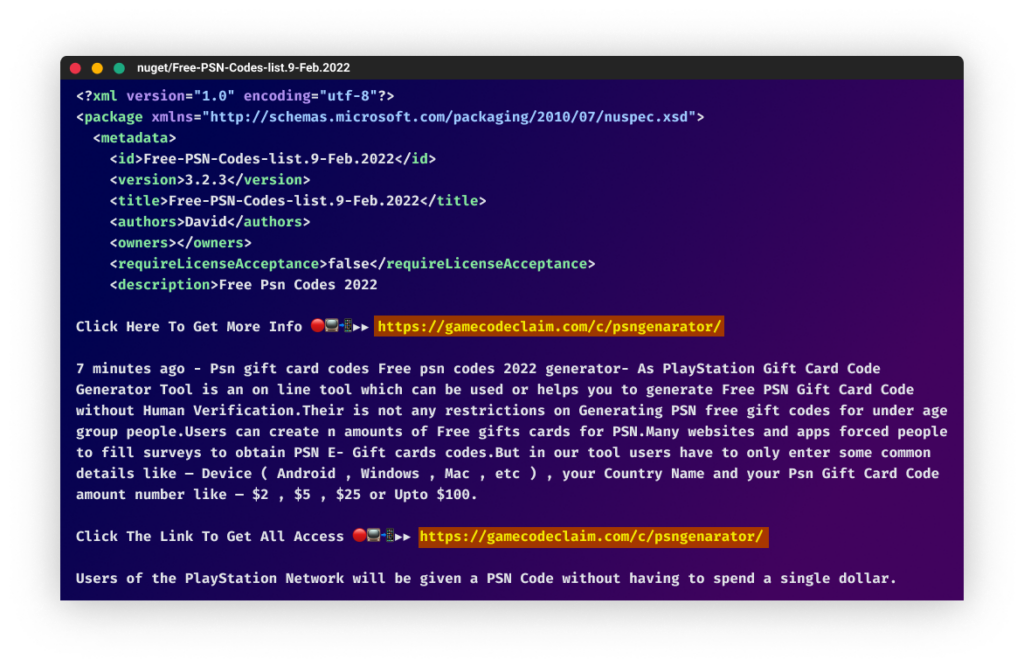
Phishing Sites in Package Description
The attackers used a large number of packages with names related to hacking, cheats, and free resources to promote their phishing campaign. Some of the package names included “free-steam-codes-generator,” “yalla-ludo-diamond-hack,” “a3-still-alive-hack-diamonds”, and “project-makeover-hack-gems.” These names were designed to lure users into downloading the packages and clicking on the links to the phishing sites.
The descriptions of all the packages we found contained links to phishing sites. The threat actors behind this campaign likely wanted to improve the search engine optimization (SEO) of their phishing sites by linking them to legitimate websites like NuGet. This highlights the need to be cautious when downloading packages and only to use trusted sources.
The messages in these packages attempt to entice readers into clicking links with promises of game cheats, free resources, and increased followers and likes on social media platforms like TikTok and Instagram.
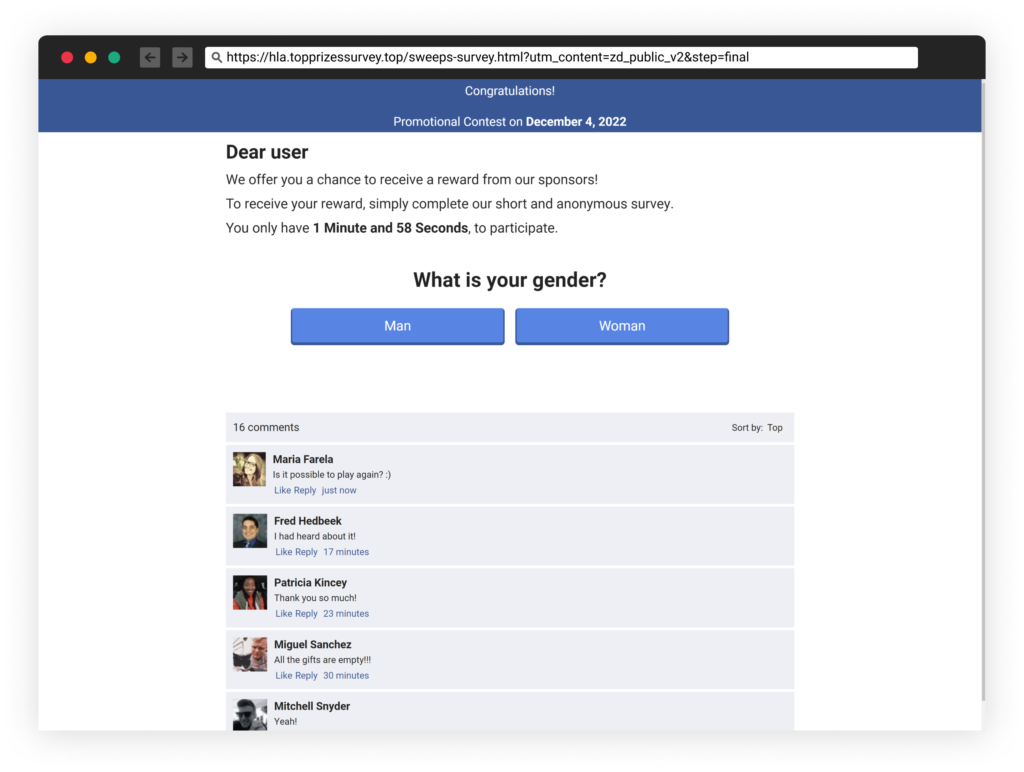
The phishing campaign linked to over 65,000 unique URLs on 90 domains, with each domain hosting multiple phishing webpages under different paths. The deceptive webpages are well-designed and, in some cases, even include fake interactive chats that appear to show users receiving the cheats or followers they were promised.
These chats will even respond to messages if the reader chooses to participate, but these are all automated and fabricated. This highlights the need for caution when interacting with links in packages and the importance of only using trusted sources.
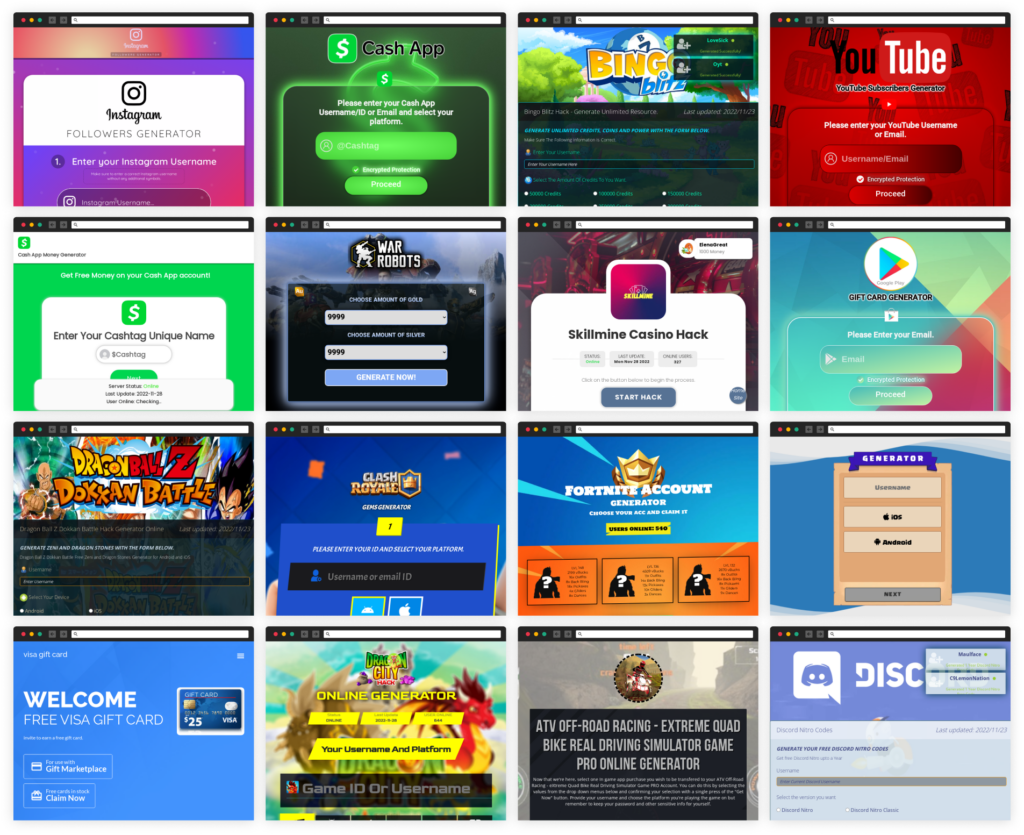
The websites included built-in fake flow that pretended to process data and generate the promised “gifts.” However, this process most of the time failed, and the victim was then asked to enter a “human verification” phase that involved multiple sites referring the user from one to another. These sites included surveys that asked the user to respond to various questions, leading to additional surveys or eventually to legitimate eCommerce websites. This shows the importance of being cautious when interacting with links in packages and only using trusted sources.
Referrals Rewards
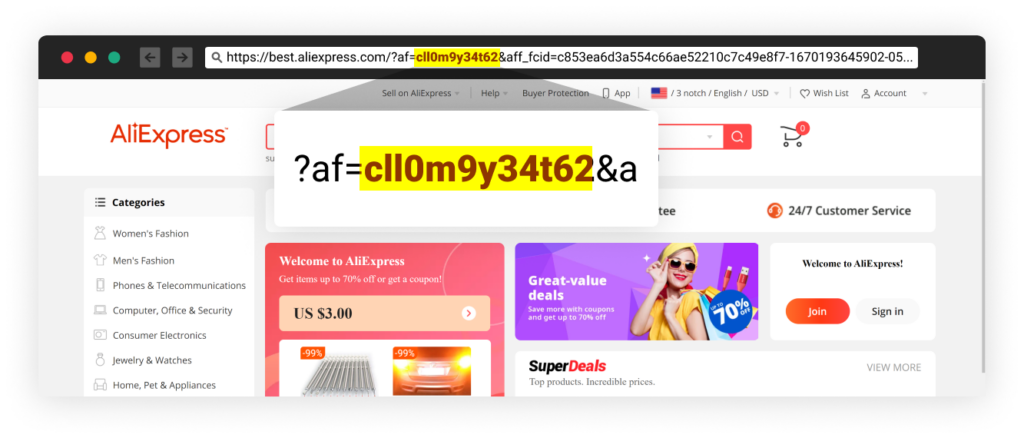
While investigating the phishing websites, we noticed that some of them redirected to eCommerce websites with referral IDs. For example, one of our experiments resulted in being redirected to AliExpress, one of the world’s largest online retail platforms. Like many other retail websites, AliExpress offers a referral program that rewards members for referring new customers to the platform.
If the threat actors refer their victims to AliExpress and they make a purchase, the threat actors’ account will receive a referral reward in the form of a coupon or store credit. This highlights the potential financial gain for threat actors who engage in phishing campaigns like this one.
Conclusion
These attackers invested in automation in order to poison the entire NuGet, PyPi, and NPM ecosystem with 144,294 packages. This allowed them to publish a large number of packages in a short period of time, making it difficult for the different security teams to identify and remove the packages quickly. Automating the process also allowed the attackers to create a large number of user accounts, making it difficult to trace the source of the attack. This shows the sophistication and determination of these attackers, who were willing to invest significant resources in order to carry out this campaign.
The battle against threat actors poisoning our software supply chain ecosystem continues to be a challenging one, as attackers constantly adapt and surprise with new and unexpected techniques.
In order to better defend against these threats, Checkmarx and Illustria have teamed up to combine their research efforts. This collaboration led to the discovery of a significant anomaly in the NuGet ecosystem.
By working together, we can stay one step ahead of attackers and keep the ecosystem safe. We believe this kind of collaboration is crucial in the fight against software supply chain attacks, and we will continue working together to protect the open-source ecosystem.
List of Packages
The scale of this phishing campaign is significant, and you are welcome to download the full dataset hosted on GitHub Gist (11mb)
This will allow you to further analyze the data and gain a better understanding of the scope and nature of the attack.
If you would like access to the original metadata or samples from this phishing campaign, please feel free to send an email to supplychainsecurity@checkmarx.com. Our team will be happy to provide you with the information you need.
IOC
In total, we analyzed over 65,000 unique URLs (click to get the full list), which we were able to reduce to approximately 90 domains. (A link to the full list is provided.) This shows the scale of the phishing campaign and the effort that was required to identify and analyze all of the URLs involved.
- tinybit[.]cc
- gamecoins[.]codes
- gamecodeclaim[.]com
- gamesapp[.]pro
- playersworld[.]xyz
- lucymods[.]com
- redirekt[.]in
- rebrand[.]ly
- gluegames[.]xyz
- igetforfree[.]com
- techdoy[.]com
- gamemasters[.]xyz
- fabgames[.]xyz
- knightmods[.]com
- gamehunters[.]win
- getfreegem[.]com
- betabuff[.]xyz
- gamesconquest[.]xyz
- gamersahead[.]com
- gamedip[.]xyz
- bizgames[.]xyz
- gamedips[.]xyz
- gamedips[.]com
- tapasgaming[.]xyz
- iwantforfree[.]com
- gainforfree[.]com
- bigmouse[.]club
- flamingame[.]com
- codesrbx[.]com
- free-albums[.]org
- lootcodes[.]com
- madgames[.]xyz
- gopremium[.]win
- giftboxfree[.]com
- cheersgamers[.]com
- gamervalvet[.]com
- gamesflow[.]xyz
- nastygames[.]xyz
- gameysky[.]xyz
- buxx[.]site
- gamerblind[.]com
- gamemasters[.]xyz
- gamecodeclaim[.]com
- wikiredeem[.]com
- codefy[.]xyz
- gaminghorn[.]com
- hackcheatsgenerators[.]com
- coub[.]com
- wbld[.]xyz
- arcades[.]tech
- gamerscrew[.]xyz
- kaciestarrtriplett[.]com
- gopremium[.]win
- vipgamesgen[.]com
- freerobux[.]best
- rbxt[.]site
- boom-beach-free-diamonds[.]com
- gamecheats[.]win
- dragon-city-free-gems[.]com
- getfortskins[.]com
- unlocker[.]cc
- webstoreusa[.]net
- sbld[.]xyz
- newsdashes[.]com
- chatgamings[.]com
- m[.]vegas7games[.]com
- giftcardsking[.]xyz
- nancymarkle[.]com
- g4ming[.]cc
- justpremium[.]xyz
- kachifpro[.]info
- ocean-of-hacks[.]com
- appmobileforce[.]com
- gemtoon[.]com
- cheersgamers[.]compubg
- techiesbay[.]com
- supergame100[.]com
- vegas7games[.]pro
- windmod[.]icu
- gamerslab[.]org
- smash[.]gg
- bandicam[.]com
- onergfx[.]xyz
- wefunder[.]com
- flamingame[.]comproject
- devices[.]by
- gametown[.]xyz
- gainforfree[.]compubg
- imv[.]quest
- spotifyplus[.]pro
- thenewsref[.]com
- correlsense[.]com
- instagramhackonline[.]com