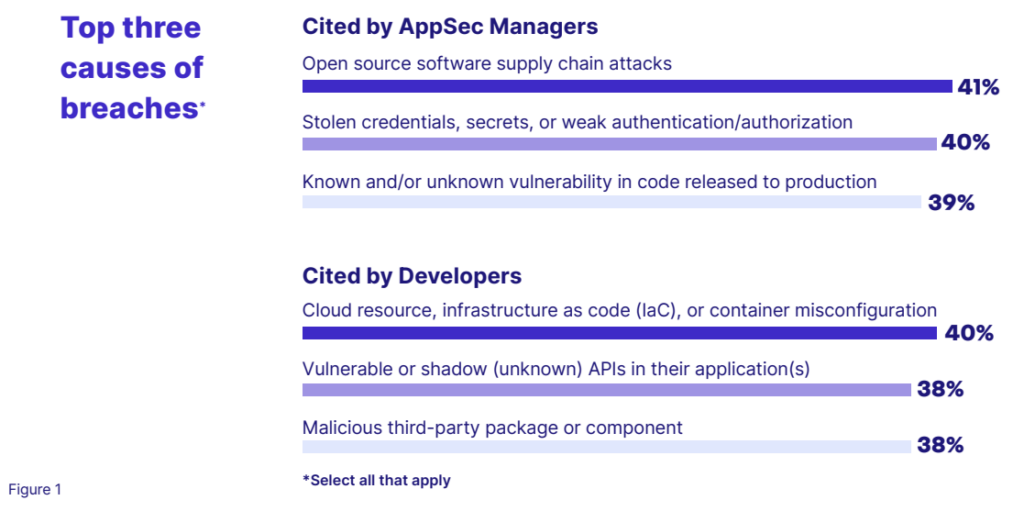
Checkmarx published our annual ‘Global Pulse on Application Security‘ report yesterday, and there’s a lot to talk about. Figure 1 [below] is actually my least favorite statistic, because it really shows how hard it is to protect an application today. There are just too many ways in which applications can be, and are, breached. This is obviously a problem. It’s a problem for an organization whose business is impacted by a breach. But it’s also a problem for people whose jobs it is to develop and/or secure these applications.
As I walk around the RSAC show floor today, I see the word, “platform,” everywhere. Every security vendor has a “platform.” Everybody’s talking about their “platform.” I’m sure that many of you have a similar reaction — this is a word that has lost its meaning. Admittedly, we also talk (a lot!) about our Checkmarx One™ Application Security Platform. So what does “platform” mean to us? And what should it mean to you?
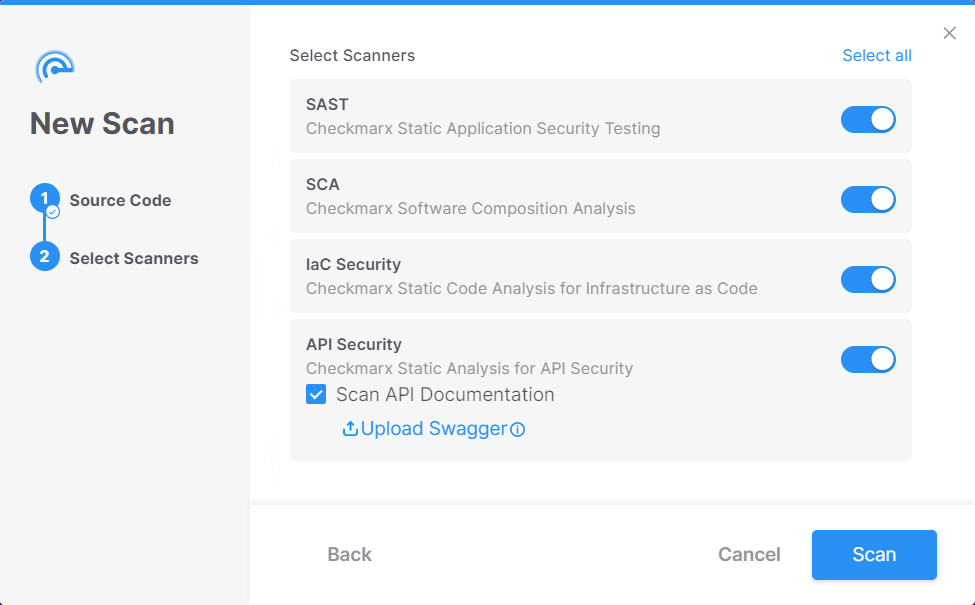
When we look at how you develop and secure your applications, our job is to make your job easier. So our platform combines all of the different tools you need to secure your application development, including SAST, SCA, supply chain security, API security, Infrastructure-as-Code (IaC) security, and container security. You can trigger all of these through a single scan. You can see and triage all your vulnerabilities in one place. You can deploy everything more easily and automate across your applications, with a single set of SDLC integrations. And you can make it easier for your developers to fix things, with IDE integration, feedback tool integration, PR decoration, and more.
Our platform is also how we roll out new products and capabilities. When we launch a new product, it’s automatically incorporated into your existing workflows. When we release new features, you automatically get them in your existing products. And today, we’re introducing a number of new and updated products and capabilities across our platform as part of our April 2023 platform launch.
Dart and Flutter support
Programming language support is #8 on our Top 10 Key Considerations when choosing a SAST solution as part of an AppSec platform. Most organizations actually have a broad requirement, from current languages you’re coding with today, to the long tail of older languages in your legacy applications, to future languages that you don’t know about yet.
With this release, Checkmarx SAST introduces the industry’s first support for Dart and Flutter, two of the fastest growing client-side programming languages and application development kits on the market today. Dart and Flutter support continues our commitment to have the broadest language support on the market, and helps you build modern digital experiences that stretch across platforms but are increasingly driven by mobile.
Private packages
Software composition analysis (SCA) has traditionally focused on open-source risks, including license risks and known vulnerabilities. More recently, Checkmarx introduced detection of malicious packages in open-source software as the second step in software supply chain security (with SBOM generally regarded as the first step).
Now, we’re introducing support for private packages — software packages and libraries that are not publicly available, typically stored in private package repositories or internal registries. Checkmarx SCA can now scan and analyze private packages and identify vulnerabilities that may exist within them, providing organizations with a comprehensive view of their software stack and broadening what’s typically included in software composition analysis.
You can read more about Private Packages on Thursday in a blog post from our of Head of Product, Steve Boone.
Exploitable path for C#
Is a vulnerability actually exploitable? Every SCA solution can tell you if a vulnerability is present in an open-source package used by your application, but that doesn’t mean it’s exploitable.
When we talk about “platform” at Checkmarx, we talk a lot about synergies between the different AST solutions that we offer on our platform. Exploitable path is a really cool feature that combines the insight from Checkmarx SAST and SCA products, and tells you when your proprietary code actually calls vulnerable code in an open-source package. This is a powerful feature that relies on having SAST and SCA capabilities not just on the same platform, but talking to each other in useful ways.
With this release, Checkmarx SCA adds C# to the list of supported programming languages where this feature is available.
SCA available for all developers in Visual Studio Code
For developers using Visual Studio Code, Checkmarx has always offered a Visual Studio plugin that brings the results of Checkmarx One (SAST, SCA, and IaC) scans directly into your IDE. Now, we’re making Checkmarx SCA available for free through the Visual Studio plugin, so that all developers (regardless of whether you’re a Checkmarx customer) can scan and analyze their open-source packages for vulnerabilities.
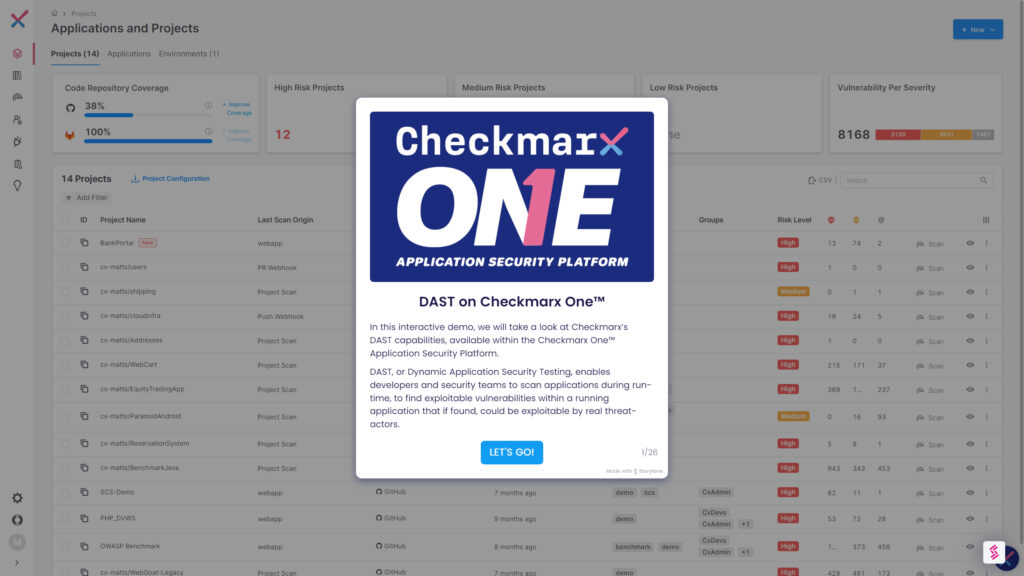
New DAST offering
For organizations looking to test throughout your SDLC, Checkmarx is bringing our DAST offering directly onto Checkmarx One. This means that you can now scan your proprietary code using SAST on the same platform that you use to scan your compiled applications with DAST. Enabling common integrations means that both SAST and DAST scans can be automated as part of your SDLC. More importantly, you can see all of your vulnerabilities in one place, triage for your developers using the same workflow, and send to them to fix using the same feedback tool integrations (e.g., JIRA). You can read more about Checkmarx DAST in this blog post by Andrew Schmit, and see it in action here.
Easier shadow API detection
Last August, we introduced the industry’s first “shift left” API Security solution that identified API vulnerabilities in code, rather than waiting for applications to be built and deployed. One of the central advantages was that we could scan proprietary code to discover and inventory your API endpoints defined in code, and compare that to the list of documented APIs, and identify your shadow APIs before they get out to production.
With the April 2023 platform launch, we’re making it easier to do so by allowing you to set up API documentation scanning as part of your unified scans for any software project. You can see Checkmarx API Security in action here.
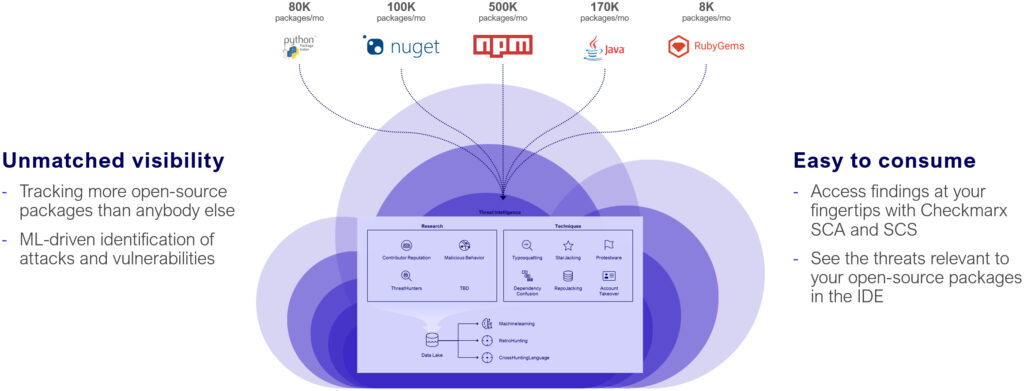
Supply Chain Threat Intelligence
In case you missed it, Checkmarx announced the availability of our Supply Chain Threat Intelligence offering back in January. Supply Chain Threat Intelligence takes all of our latest threat intelligence on malicious packages, used by our security researchers to identify attackers such as RED-LILI and Lofygang, and makes them available to customers via a simple API call. This allows you to build that intelligence into your automated SDLC workflows, even if you’re not a Checkmarx One customer.
New secrets detection engine
Finally, Checkmarx is releasing a new secret detection engine, aptly named Too Many Secrets (2MS). In the context of applications, secrets are sensitive information such as passwords, API keys, cryptographic keys, and other confidential data that an application needs to function but should not be exposed to unauthorized users. As part of the development process, developers often use collaboration tools like Confluence to share secrets necessary to develop an application. And then, because we all forget about things, these secrets can be accidentally published and disclosed.
2MS is an open-source project dedicated to helping people protect their sensitive information like passwords, credentials, and API keys from appearing in public websites and communication services. Read more about 2MS tomorrow in a blog post from its product manager, Bryant Schuck, and download the project yourself from GitHub.
Learn more
We’re excited to introduce these new capabilities as part of our April 2023 Platform Launch, as we continue to enhance our platform to make your jobs easier. For Checkmarx customers, please reach out to your account team to learn more about these (and more).
AppSec
English
Launch
Leadership
