Summary
AI cybersecurity solutions use artificial intelligence and machine learning to detect, prioritize, prevent, and respond to threats across applications, endpoints, networks, cloud environments, and security operations. Because the category is broad, the right solution depends on whether your main priority is application security, SOC efficiency, endpoint defense, or software supply chain risk.
What Are AI Cybersecurity Solutions?
AI cybersecurity solutions (often called AI cybersecurity tools or AI-powered cybersecurity solutions) use machine learning and automation to help organizations detect, prevent, and respond to threats across applications, endpoints, networks, and cloud environments.
Unlike traditional approaches that depend heavily on static rules and known signatures, AI systems learn patterns from large volumes of telemetry to identify suspicious behavior, prioritize risk, and recommend next actions faster.
The most effective solutions combine automation with governance – clear evidence, explainable alerts, policy controls, and human approval for high-impact actions – so teams move faster without losing control.
AI Cybersecurity Solutions at a Glance (quick shortlist)
If you want a fast starting point, the tools below cover the most common AI-driven security use cases across AppSec, endpoint protection, and SOC automation.
Keep reading for the full tool-by-tool analysis (key features, limitations, and where each solution fits best).
| Tool | Best for | One-line differentiator |
|---|---|---|
| Checkmarx One Assist | Enterprise AppSec teams securing high-velocity delivery | Unified code-to-cloud AppSec platform with AI assistance across IDE, CI/CD, and governance |
| Snyk AI Workflows | Dev-first AppSec programs | AI-assisted developer workflows and fix guidance embedded across SDLC |
| Mend AI Native AppSec | AppSec teams focused on supply-chain risk | Dependency-centric AppSec with automation for prioritization and remediation workflows |
| CrowdStrike Falcon | Endpoint security at scale | AI-driven threat detection and response across endpoints with strong telemetry |
| Microsoft Sentinel | SOC teams standardizing on Microsoft | Cloud-native SIEM with AI-assisted detection and investigation workflows |
| Cortex XSOAR | SOC automation and incident response | SOAR playbooks and orchestration designed to speed triage and response |
Not all AI cybersecurity solutions solve the same problem. Some focus on securing software during development, some improve endpoint and network defense, and others accelerate SOC detection and response.
For organizations building software at speed, AI-powered application security is the most relevant category because it helps prevent vulnerabilities before they reach production.
Benefits of AI-Based Cybersecurity Solutions
AI cybersecurity solutions provide several key advantages over traditional security approaches. By leveraging automation, adaptability, and advanced data analysis, they help organizations strengthen their defense posture and respond faster to emerging threats.
Benefits of AI cybersecurity solutions in application security:
- Early vulnerability detection: AI models can analyze source code, dependencies, and infrastructure configurations in real time, catching vulnerabilities during development—before they reach production.
- Continuous runtime monitoring: AI tools establish behavioral baselines and detect anomalies in real-time, flagging suspicious application activity that traditional tools might miss.
- Reduced false positives: By learning normal application behavior, AI systems filter out noise and reduce false alerts, allowing security teams to focus on real threats.
- Faster remediation: AI-driven remediation tools can suggest or apply fixes automatically, accelerating patching cycles and reducing time-to-fix.
- Protection against AI-generated code flaws: As generative AI tools are used in development, AI security platforms help detect insecure patterns that might be introduced by these tools.
Benefits of AI cybersecurity solutions in endpoint security:
- Real-time threat detection: AI continuously monitors endpoint activity (processes, file access, and network behavior) to identify malicious patterns as they happen.
- Protection against zero-day attacks: AI models recognize previously unseen threats by identifying behavioral anomalies, closing the gap left by signature-based solutions.
- Automated incident response: When a threat is detected, AI can trigger predefined actions like quarantining devices or isolating network segments without human intervention.
Benefits of AI cybersecurity solutions in the security operations center (SOC):
- Alert prioritization: AI filters and scores alerts based on severity and context, helping analysts focus on incidents that matter most.
- Automated triage and investigation: AI correlates logs, indicators of compromise, and threat intelligence to provide context-rich summaries and accelerate investigations.
- Faster incident response: AI-powered SOAR tools execute automated playbooks to contain threats quickly, reducing mean time to detect (MTTD) and mean time to respond (MTTR).
- Threat hunting support: AI helps uncover hidden threats by sifting through large datasets, highlighting patterns humans may overlook.
Types of AI-Powered Security Platforms
AI-Powered Application Security
AI-powered application security solutions use machine learning and agentic automation to analyze source code, open-source dependencies, infrastructure as code, APIs, containers, and runtime context. Their goal is not just to find issues, but to prioritize the risks that matter most and accelerate secure remediation across human-written, AI-generated, and legacy code.
These systems can identify vulnerabilities, insecure libraries, and misconfigurations during software development and after deployment. By learning from millions of known attack patterns and coding errors, AI-driven tools flag issues that may expose software to exploitation, helping developers address problems before code reaches production.
In production, AI-powered application security platforms continuously monitor application behavior for signs of compromise. Unlike static scanners, these tools adapt to real-world conditions, learning how apps work and establishing a baseline for healthy operation. When anomalies occur, such as unexpected data flows or function calls, the system alerts security teams or automatically triggers countermeasures. This approach shortens the window of exposure and supports rapid remediation in cloud-native, containerized, and serverless environments.
AI-Powered Endpoint Protection
AI-powered endpoint protection platforms defend laptops, desktops, mobile devices, and servers from advanced threats. These systems analyze local activity, including files, processes, network connections, for suspicious behavior that may indicate malware, ransomware, or lateral movement by attackers. Machine learning algorithms can spot previously unknown threats by recognizing deviant patterns, while policy-driven automation enforces preventative controls or initiates quarantines.
Over time, AI reduces false positives by refining its understanding of legitimate versus malicious behavior in specific environments. This benefit is critical for organizations with diverse remote workforces and BYOD (bring your own device) policies. The result is stronger, more adaptive endpoint defense with minimal intervention from users or IT staff. AI-enabled endpoint platforms also integrate easily with SIEM and SOAR systems to coordinate threat response across the broader cybersecurity ecosystem.
AI-Powered SIEM and SOAR Platforms
SIEM (Security Information and Event Management) and SOAR (Security Orchestration, Automation, and Response) platforms aggregate, correlate, and analyze data from across the organization. AI enhances these platforms by providing faster and more accurate threat detection, context enrichment, and event prioritization. Machine learning models can sift through millions of logs, alerts, and telemetry entries to find connections that manual analysis would miss, helping security teams quickly zero in on real risks.
SOAR capabilities automate playbooks, enabling rapid response to threats without human intervention for routine incidents. AI-driven SOAR platforms can distinguish between benign anomalies and true attacks, reducing unnecessary escalations. They also integrate with a wide array of security tools, including firewalls, identity providers, threat intelligence feeds, to provide end-to-end visibility and response coordination. This holistic approach empowers security operations centers to act promptly and consistently across diverse IT environments.
Notable AI Cybersecurity Solutions
To compile the notable AI cybersecurity solutions below, we focused on tools that are widely adopted and consistently used in real-world security programs – not just those that market “AI” features.
Each solution was evaluated on practical criteria that matter to AppSec and security leaders: coverage of the target domain (application security, endpoint, or SOC), the quality of detection and prioritization (signal-to-noise, context, and validation), workflow fit (IDE/CI/CD or SIEM/SOAR integrations), governance and auditability (explainable outputs, policy controls, and approvals), scalability and performance, and ecosystem maturity (documentation, support, and community).
AI-Powered Application Security
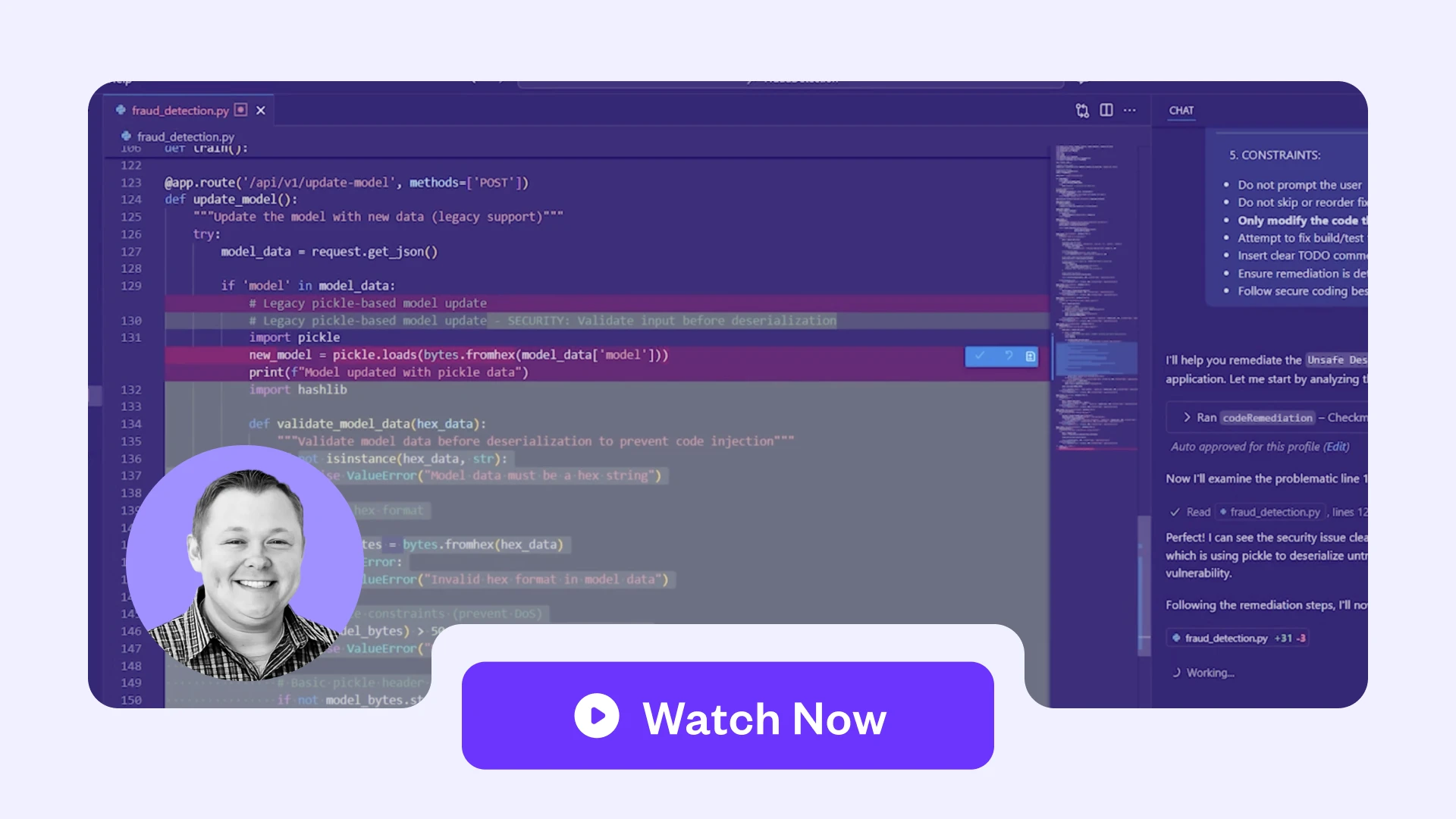
1. Checkmarx One Assist

Best for: Enterprise teams that need AI-powered application security and software supply chain protection across modern, legacy, and AI-generated code.
Key strengths: A unified Checkmarx One platform that correlates code-to-cloud AppSec signals (SAST, SCA, IaC, API, DAST, containers) with role-specific agents (Developer Assist, Policy Assist, Insights Assist) to reduce alert fatigue and speed up remediation.
Things to consider: Purpose-built for application security – pair with dedicated endpoint/SIEM tools if those are primary requirements, and plan adoption across dev workflows to get the full value.
Checkmarx One Assist is a family of agentic AI AppSec agents: Developer Assist, Policy Assist, and Insights Assist. Powered by the Checkmarx One platform and its unified telemetry, these agents live where teams work: the IDE, CI/CD pipelines, and executive dashboards. Together they prevent and remediate vulnerabilities in real time, standardize security policies at scale, and give leadership a live, risk-based view of the entire application portfolio so enterprises can ship AI-era software faster without losing control.
Checkmarx One Assist provides CISOs and Security Leaders continuous, portfolio-level visibility into application risk, policy adherence, and remediation performance via Insights Assist, and links AppSec outcomes to business objectives with trend data and live posture views drawn from the entire Checkmarx One platform. For AppSec leaders and security teams, Checkmarx One Assist orchestrates and standardizes AppSec policies across diverse pipelines, minimizing manual gatekeeping and reducing noise.
Key features include:
- Secure coding in the IDE: Developer Assist prevents and fixes vulnerabilities as code is written, including AI-generated code, across SAST, SCA, IaC, containers, and secrets.
- Policy enforcement in CI/CD: Policy Assist continuously evaluates code, configurations, and dependencies in pipelines, automatically enforcing AppSec policies, SLAs, and risk thresholds while reducing alert noise.
- Portfolio-level insights and governance: Insights Assist aggregates signals from Checkmarx One to surface posture, trends, and exceptions for leadership, enabling risk-based planning, reporting, and investment decisions.
- End-to-end AI threat coverage: The agents use shared intelligence from Checkmarx One: spanning applications, open-source packages, containers, cloud, and malicious package telemetry: to protect against AI-driven threats and software supply chain risk.
- Faster adoption and less friction: Role-specific agents fit naturally into developer, AppSec, and leadership workflows, accelerating value realization and helping organizations scale secure development practices without large process overhauls.
Key differentiators include:
- Agentic AI woven through a unified platform: Each Assist agent is backed by the same unified, cloud-native AppSec platform that centralizes scanning, prioritization, and remediation across SAST, SCA, IaC, API, container, and supply-chain security.
- Role-aware design: Developer, Policy, and Insights agents are purpose-built for their users: developers, AppSec and DevOps teams, and security leaders: addressing real DevSecOps friction points rather than generic LLM use cases.
- Context-rich, policy-aware actions: Agents draw on Checkmarx ASPM, policy rules, and business context to make decisions that align with enterprise standards and can be audited and tuned.
- Coverage from code to cloud: Checkmarx One Assist leverages data from code repositories, build systems, registries, runtime and cloud insights, as well as malicious package intelligence, to understand and act on risk at every layer.
- Recognized leadership in agentic AppSec: Independent analysts highlight Checkmarx as an early leader in applying AI agents across secure code creation, policy enforcement, and risk oversight, with a strong track record in enterprise AppSec.
- PR-native triage & remediation: Checkmarx Triage & Remediation Assist runs natively in GitHub pull requests to classify findings by real-world risk and generate reviewable remediation PRs/diffs with governed, auditable decisioning.
Secure Code at AI Speed
Prevent More. Remediate Faster.
Built for modern development. Built for real security. Proactively protect software from AI-driven and software supply chain threats.rn
See it in Action2. Snyk AI Workflows

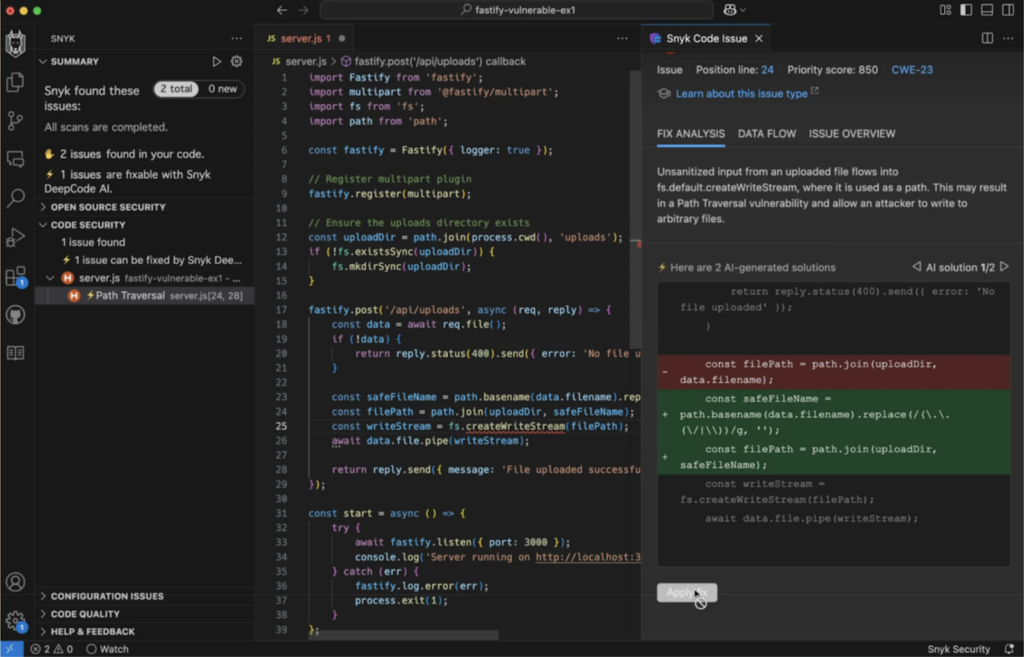
Best for: Development teams that want embedded, AI-driven security directly inside the SDLC and developer workflows.
Key strengths: Deep IDE and CI/CD integration with automated fix generation and policy-based guardrails.
Things to consider: Setup complexity and alert noise can require tuning and experienced AppSec resources.
Snyk AI Workflows deliver a full-stack application security solution tailored for modern, AI-driven development. By embedding AI capabilities throughout the software development lifecycle (SDLC), Snyk enables development and security teams to collaborate and ship secure code faster. It provides real-time coding assistance with proactive vulnerability detection and policy enforcement.
Key features include:
- AI-powered developer assistance: Snyk Assist provides in-context guidance and secure coding recommendations directly within development workflows.
- Autonomous fix generation: Snyk Agent Fix suggests and validates code fixes automatically, helping developers remediate issues quickly without breaking functionality.
- Secure AI-native development: Snyk Studio integrates with AI development tools to embed security from the start, preventing vulnerabilities during early development stages.
- Policy-based guardrails: Snyk Guard uses dynamic, risk-aware policies to enforce security standards in real time and adapt to changing risk levels.
- Full SDLC coverage: AI workflows are integrated across the entire lifecycle, from code to deployment, supporting scalable, enterprise-wide security programs.
Limitations (as reported by users on G2):
- Complex configuration: Users report that configuring Snyk can be difficult, with complex setup and policy management that may require additional tools to get the needed visibility.
- High volume of false positives: Many users mention excessive false positives, which makes alert management harder and increases the effort required to track real issues.
- Alert overload: Due to the number of findings and policy overrides, teams can struggle to manage and prioritize alerts effectively.
- Tool complexity: Managing scans, alerts, and policies is described as complex, especially for teams new to application security tooling.
- Command line usability issues: Some users find the command line interface challenging and note that it lacks key functionality without relying on third-party tools.
- Product bugs: Users report encountering bugs that affect reliability and day-to-day use of the platform.
- Customer support challenges: Several reviews highlight slow response times and unhelpful support, with unresolved issues even after escalation.
- Pricing concerns: Some users question the value of the platform, particularly when additional tools are needed to compensate for missing or unreliable features.
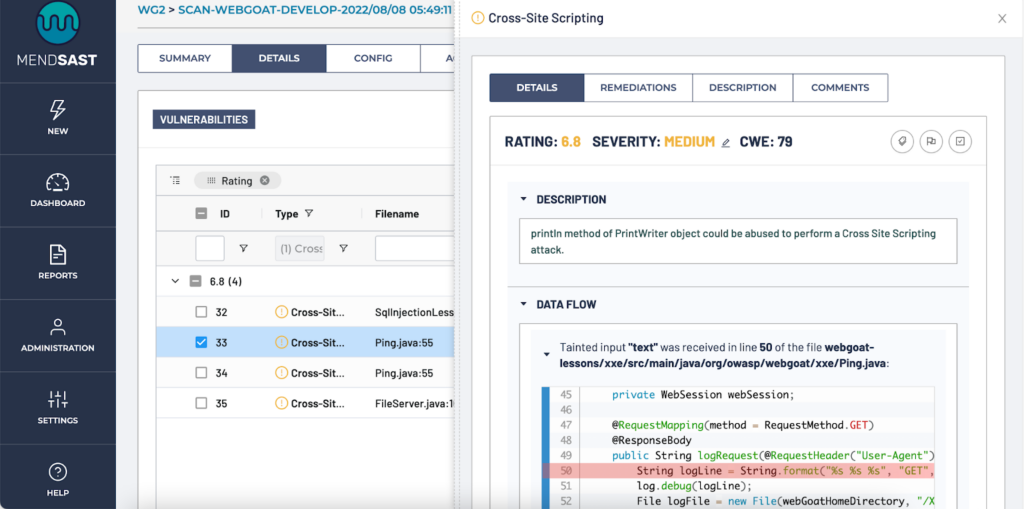
3. Mend AI Native Application Security Platform

Best for: Organizations building AI-enabled applications that need unified security across code, open source, containers, and AI assets.
Key strengths: Dual-mode AI scanning with automated remediation and dedicated AI asset governance.
Things to consider: Higher pricing and mixed integration experiences may impact overall value in some environments.
The Mend AI Native Application Security Platform is designed to secure AI-driven software development from code creation to deployment. Built specifically for environments leveraging AI-generated code and models, the platform provides integrated protection across the full stack: Source code, open source components, containers, and AI assets.
Key features include:
- Dual-mode code scanning: Combines a fast AI-tuned scan at code creation with deep SAST and SCA analysis at commit to detect and verify issues early.
- AI-powered remediation: Uses automation and AI to fix critical vulnerabilities at scale, reducing time to remediation across the SDLC.
- Unified security visibility: Offers a centralized view of security posture across code, open source, containers, and AI components, eliminating operational silos.
- AI asset governance: Finds, scans, hardens, and manages all AI models, agents, and prompts, providing security teams with oversight and developers with actionable guidance.
- Automated AI risk management: Continuously discovers and assesses risks in AI components, supporting proactive governance and policy enforcement.
Limitations (as reported by users on G2):
- High pricing: Users report that Mend is relatively expensive, with some feeling that the cost is not fully justified by the features provided.
- Integration challenges: Despite generally easy setup for basic use cases, some users experience integration issues, noting that integrations are not as seamless as expected.
- Limited cloud integration depth: Users mention that cloud integration capabilities feel limited, particularly when compared to the platform’s pricing.
- Perceived value concerns: The combination of higher cost and integration limitations leads some users to question the overall value for money.
- Inconsistent integration experience: While many users find integrations straightforward, others report uneven quality depending on the environment or tools being connected.
AI-Powered Endpoint Protection
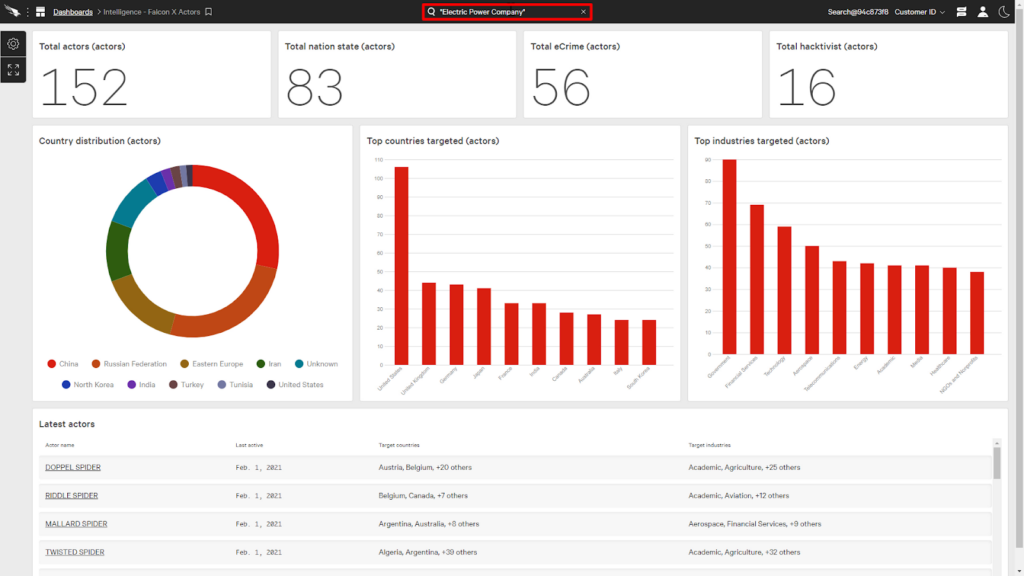
4. CrowdStrike Falcon platform

Best for: Large enterprises seeking AI-driven endpoint detection and response with advanced automation and threat intelligence.
Key strengths: Strong behavioral detection, enterprise-scale telemetry graph, and AI-assisted investigation workflows.
Things to consider: Tiered licensing and UI complexity can increase cost and operational overhead.
The CrowdStrike Falcon platform is an agentic security platform built to defend against threats in the age of AI. It integrates AI-native tools, security agents, and data intelligence into a unified system that protects the entire AI ecosystem, from data and models to agents and infrastructure.
Key features include:
- Enterprise graph data layer: Unifies telemetry across the enterprise to create a dynamic, AI-ready data model accessible through a common query language.
- Mission-ready AI agents: Automates core security workflows to reduce analyst workload and accelerate triage, investigation, and response.
- Charlotte AI AgentWorks: A no-code platform for building, orchestrating, and deploying AI security agents using natural language.
- Natural language interface: Enables interaction with security data through natural language queries and role-based dashboards.
- Agent collaboration framework: Connects AI agents, systems, and data sources to centralize control and enrich investigation context.
Limitations (as reported by users on G2):
- High cost and tiered licensing: Users frequently mention that CrowdStrike Falcon is expensive, with many advanced capabilities requiring separate licenses, increasing overall cost and complexity.
- Complex user interface: The interface is described as tricky and sometimes confusing, making navigation across dashboards and features harder than expected.
- Steep learning curve: Due to complex terminology and a feature-rich UI, new users may need time and training to become effective with the platform.
- Feature gaps in base packages: Some essential capabilities, such as remediation actions, are not included in basic plans and require upgrades like Falcon Complete.
- Platform-specific limitations: Users report weaker detection or limited functionality on certain platforms, particularly macOS endpoints.
- False positives: While detection is strong, users experience occasional false alerts, which can create noise and require manual validation.
- Navigation and usability challenges: Managing multiple screens and workflows can slow investigations and report generation.
- Support and maintenance friction: Some users report slower support responses and difficulties during troubleshooting, updates, or uninstallation processes.
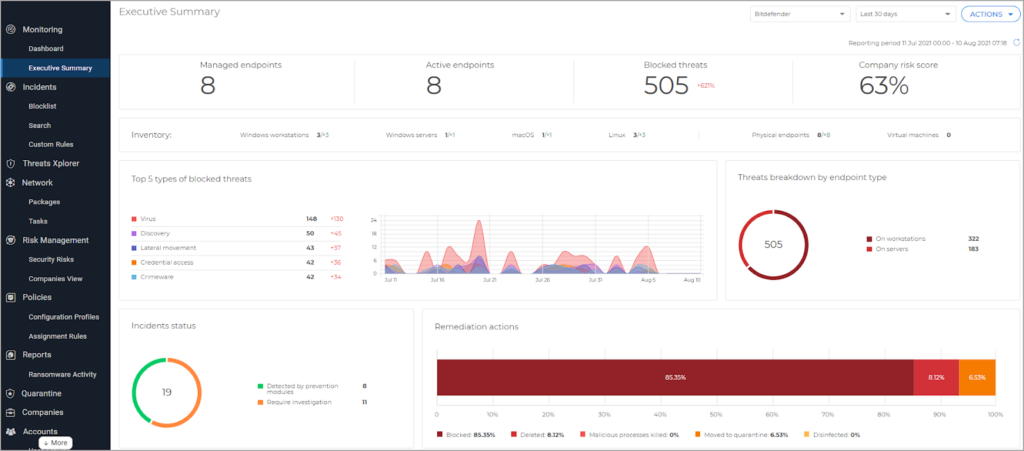
5. Bitdefender GravityZone

Best for: Mid-sized to large organizations that need layered endpoint protection with integrated risk management.
Key strengths: Multi-layered, signature-less detection with sandboxing and detailed attack forensics.
Things to consider: Interface complexity and configuration effort may slow onboarding and daily management.
Bitdefender GravityZone Business Security Premium is an all-in-one endpoint protection platform that combines proactive threat prevention, attack forensics, and risk management into a single, simplified solution. It uses layered defenses, including machine learning, behavior analysis, sandboxing, and fileless attack protection, to detect and stop sophisticated threats.
Key features include:
- Layered threat protection: Integrates machine learning, behavior analysis, sandboxing, and device hardening to detect advanced threats using a signature-less approach.
- Attack forensics and visualization: Maps attack chains and threat origins to show how incidents unfold and where response actions are required.
- Risk management module: Identifies and prioritizes risks from software misconfigurations, vulnerable applications, and unsafe user behavior.
- Fileless attack defense: Detects and blocks threats that do not rely on files, such as malicious PowerShell scripts or code injections, by analyzing processes in real time.
- Cloud-based sandbox analyzer: Detonates suspicious files in an isolated cloud environment to identify malicious behavior before execution.
Limitations (as reported by users on G2)
- Difficult navigation: Users report that finding specific settings is often unintuitive, with menus and options not located where users expect them to be.
- Complex and cluttered interface: The dashboard and administration views are described as confusing, particularly for non-technical users.
- Steep learning curve: Configuring policies, exceptions, and endpoint profiles can take time, requiring familiarity with the platform to use it effectively.
- Challenging initial setup: Some users note that the initial setup and policy configuration feel complex, especially during first-time deployment.
- Configuration tuning effort: Achieving optimal configurations, especially for developer endpoints with many small files, can require significant trial and error.
- Inconvenient updates: Users mention that some updates require system restarts, which can disrupt work during business hours.
- UX inconsistencies: Users highlight the need for improvements in overall usability and dashboard organization to simplify daily management tasks.
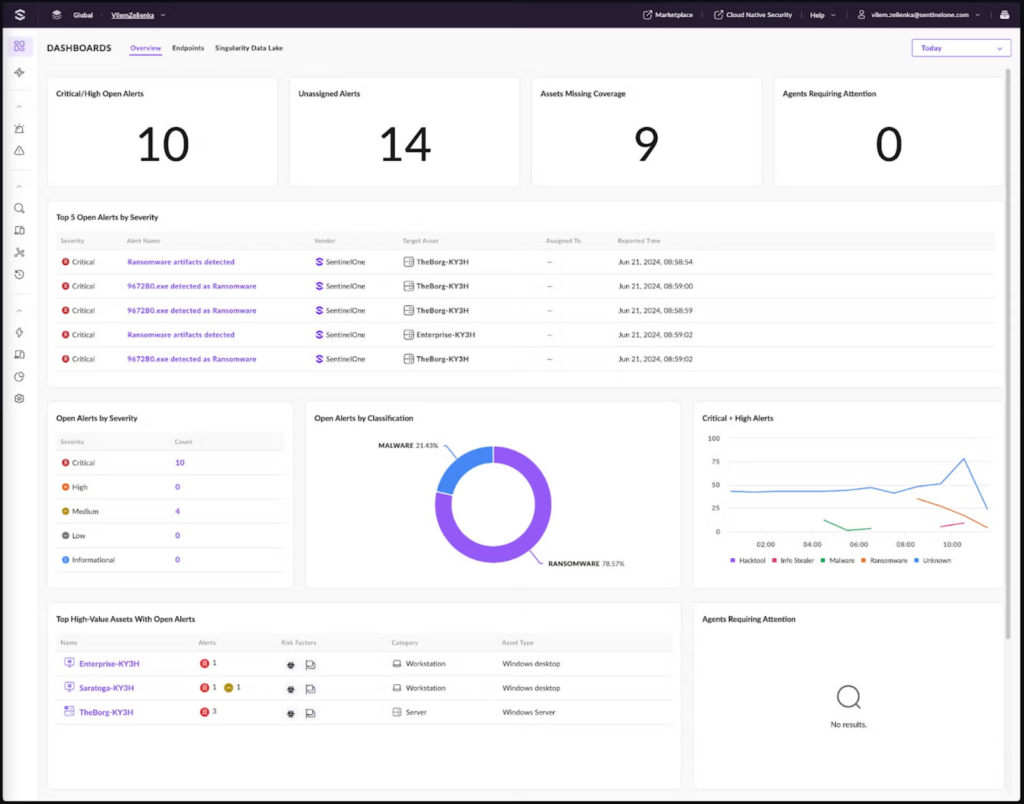
6. SentinelOne Singularity

Best for: Security teams that want unified endpoint, cloud, and identity protection with automated rollback and response.
Key strengths: Behavioral AI detection with one-click remediation and AI-augmented threat hunting.
Things to consider: Higher cost and tuning requirements to reduce false positives may require dedicated expertise.
SentinelOne Singularity Complete is an AI-powered security platform that delivers unified protection across endpoints, cloud workloads, and identities. Designed to minimize risk and reduce complexity, it combines real-time prevention, AI-driven detection, and automated response in a single, resource-efficient agent.
Key features include:
- Unified endpoint and cloud protection: Provides deep visibility and machine-speed prevention across workstations, servers, and cloud environments using a single agent.
- Behavioral AI detection: Detects ransomware, zero-day threats, and malicious patterns in real time through advanced static and behavioral AI models.
- AI-augmented threat hunting: Enhances investigations with Purple AI, enabling natural language queries, automated summaries, and self-documenting forensic notebooks.
- Automated response and remediation: Executes predefined actions or patented 1-click rollback to restore systems after an attack, reducing response time and impact.
- Full remote shell access: Supports in-depth investigation, live response, and forensic data collection directly from compromised systems.
Limitations (as reported by users on G2):
- High cost: Users frequently mention that SentinelOne Singularity is more expensive than alternative endpoint security tools, which can be a concern for cost-sensitive teams.
- Steep learning curve for advanced features: While basic usage is straightforward, advanced capabilities and workflows can feel overwhelming for new users and require time to master.
- False positives and overblocking: Some users report false positives and legitimate applications being blocked, making fine-tuning necessary after deployment.
- Limited feature coverage: Users note missing capabilities such as basic web reputation filtering and more mature mobile device protection.
- Agent and migration issues: During migrations from other EDR solutions, users experience agent-related problems, including endpoints dropping from management or applications being blocked without clear alerts.
- Alert clarity and classification gaps: Alert categorization and filtering are described as limited, which can make triage and prioritization harder in busy environments.
- Dashboard and navigation complexity: The number of dashboards and options can complicate navigation and slow down investigations.
- Customer support inconsistencies: While support is often praised, some users report slow response times or limited help for complex investigations and DFIR-related issues.
AI-Powered SIEM and SOAR Platforms
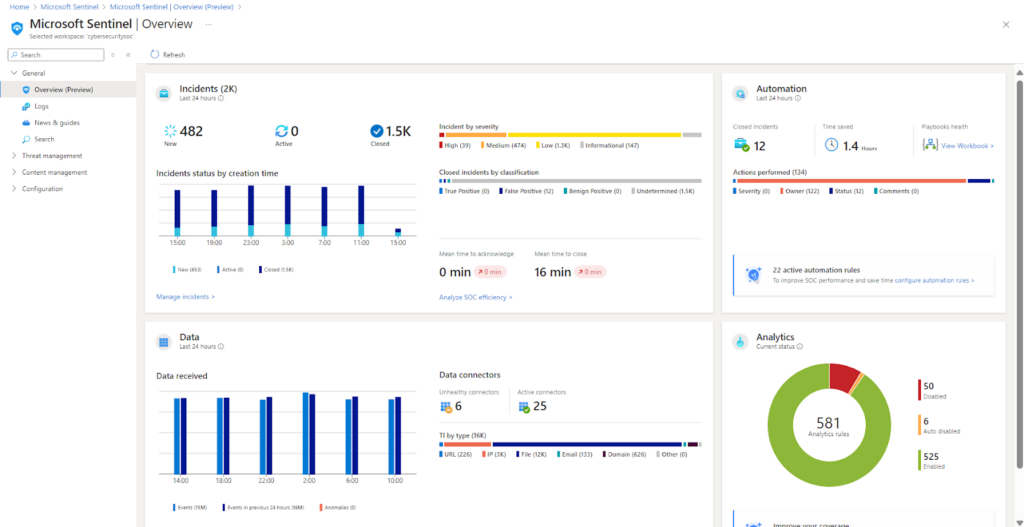
7. Microsoft Sentinel SIEM

Best for: Organizations invested in Azure or hybrid cloud environments that need scalable, cloud-native SIEM capabilities.
Key strengths: Deep Microsoft ecosystem integration with strong analytics, hunting, and automation features.
Things to consider: Pay-as-you-go pricing and KQL complexity can increase operational and cost management effort.
Microsoft Sentinel is a cloud-native SIEM (security information and event management) platform that delivers scalable, AI-powered threat detection, investigation, and automated response across hybrid and multicloud environments. Built on Azure, it collects data from virtually any source, Microsoft and non-Microsoft alike, using out-of-the-box and custom connectors.
Key features include:
- Cloud-native SIEM architecture: Built on Azure, Sentinel scales to meet the demands of modern, multicloud, and multiplatform environments without on-premises infrastructure.
- Comprehensive data collection: Supports data ingestion from Microsoft services, third-party platforms, and custom sources using connectors, Syslog, REST APIs, and CEF.
- Advanced threat detection: Uses analytics rules, threat intelligence, and MITRE ATT&CK mapping to detect real threats and minimize false positives.
- Interactive investigation tools: Enables visual root-cause analysis using entity graphs and AI-assisted investigation features.
- Proactive threat hunting: Provides hunting capabilities via Kusto queries, supports custom detection rules, and includes integrated Jupyter notebooks for advanced analysis.
Limitations (as reported by Users on G2):
- High cost at scale: The pay-as-you-go pricing model can become expensive as log ingestion volumes grow, making cost control challenging for large environments.
- Complex setup and learning curve: Initial setup, rule creation, and playbook development can be complex, often requiring training and prior knowledge of KQL.
- Alert fatigue and inefficient alerts: Users report a high volume of alerts and difficulty quickly finding relevant rules or use cases, which can slow investigations.
- User interface challenges: The interface is sometimes described as difficult to navigate, with performance and usability issues impacting day-to-day operations.
- Integration challenges with non-Microsoft tools: While possible, integrating third-party, non-Microsoft tools may require extra configuration, guides, or workarounds.
- Limited RBAC granularity: Sentinel lacks fine-grained RBAC controls at the table level, limiting access control compared to Azure Data Explorer.
- Cloud-only dependency: Sentinel is not available on-premises, which can be a limitation for organizations with strict data residency or hybrid requirements.
- Playbook creation complexity: Building and maintaining automation playbooks can be time-consuming, especially for teams new to Azure Logic Apps.
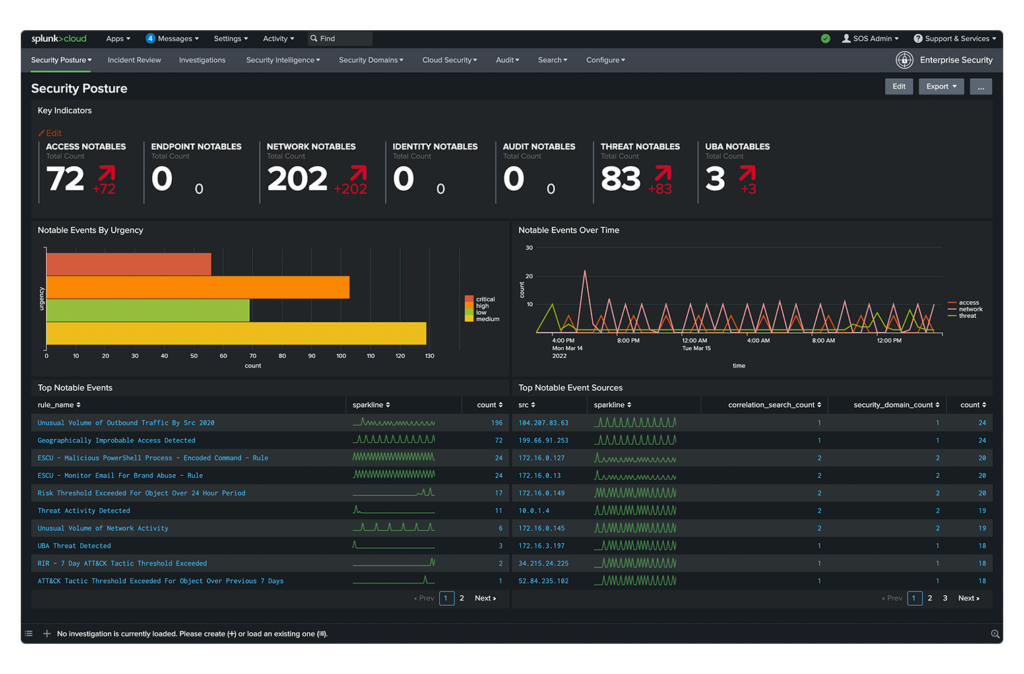
8. Splunk SOAR

Best for: Mature SOC teams looking to automate complex incident response workflows across diverse security tools.
Key strengths: Extensive third-party integrations and flexible, automation-driven playbooks.
Things to consider: Platform complexity and cost may challenge smaller or less experienced teams.
Splunk SOAR (Security Orchestration, Automation, and Response) is now a fully integrated capability within Splunk Enterprise Security, forming part of a unified SecOps platform that includes SIEM, UEBA, and AI-driven insights. Splunk SOAR automates repetitive tasks, accelerates response times, and connects tools and teams through customizable playbooks.
Key features include:
- Automated playbooks: Execute complex security actions in seconds using prebuilt or custom playbooks aligned with frameworks such as MITRE ATT&CK and D3FEND.
- Extensive tool integration: Support over 300 third-party tools and more than 2,800 actions to orchestrate workflows across existing security and IT tools without replacement.
- Visual playbook editor: Provide a no-code or low-code interface for building workflows, allowing teams to create and maintain automation logic with minimal development effort.
- Integrated case management: Enable structured incident response with shared cases, task assignments, and real-time documentation.
- Threat intelligence-driven insights: Present prioritized threat context in a centralized investigation view based on research from the Splunk Threat Research Team.
Limitations (as reported by users on G2):
- Steep learning curve: New users report that getting started can be difficult, especially for teams without prior experience in automation or SOAR platforms.
- Overall complexity: The platform is considered complex to learn and operate, with advanced features requiring time and hands-on practice to use effectively.
- High cost for smaller organizations: Users note that Splunk SOAR can be expensive, making it less accessible for small businesses with limited security budgets.
- Not always intuitive interface: Some parts of the user interface are described as unintuitive, which can slow adoption and increase onboarding time.
- Challenging initial adoption: Early usage can feel overwhelming due to the depth of functionality and configuration options.
- Customer support concerns: A few users report frustration with support when dealing with complex issues, despite responsiveness in some cases.
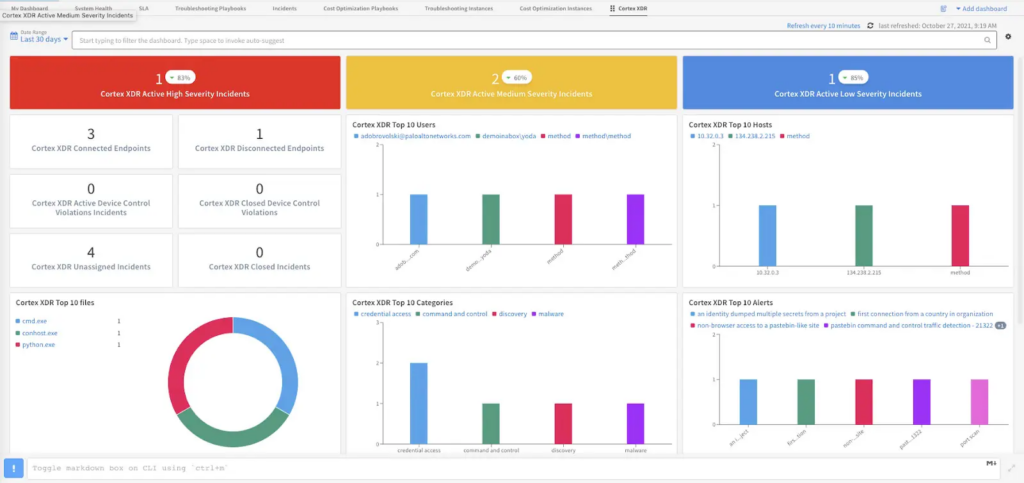
9. Cortex XSOAR

Best for: Enterprises that require highly customizable incident response orchestration with integrated threat intelligence.
Key strengths: Automation-first design with broad integration support and centralized investigation workflows.
Things to consider: Steep learning curve and ongoing management overhead can impact time to value.
Cortex XSOAR is a security orchestration, automation, and response (SOAR) platform built to streamline incident response by reducing manual effort, integrating threat intelligence, and coordinating actions across the SOC.
Key features include:
- Automation-first incident response: Offloads repetitive, manual tasks using automation packs and custom playbooks, allowing analysts to focus on high-value investigations.
- Visual playbook editor: Creates no-code automation workflows using a drag-and-drop interface, backed by thousands of prebuilt actions across integrated tools.
- Unified investigation workspace: Consolidates indicators, incident data, and threat intelligence into a single interface with built-in war rooms for real-time collaboration and reporting.
- Cross-stack orchestration: Coordinates actions across security teams, processes, and technologies to centralize incident response across the organization.
- Threat intelligence integration: Enhances alert triage and investigation by correlating external threat data with internal incident activity.
Limitations (as reported by users on G2):
- Steep learning curve: Users report that Cortex XSOAR takes significant time to learn, especially for teams new to SOAR platforms or large-scale automation.
- Operational complexity: Day-to-day usage can feel complex, with workflows and features requiring effort before teams become fully productive.
- Limited reporting customization: Reporting capabilities are seen as rigid, with users wanting more flexibility and customization options.
- Log readability issues: Logs can be difficult to review quickly due to limited window sizes, often requiring opening results in separate tabs.
- Log management friction: The interface for viewing and managing log data can slow investigations when working with large datasets.
- Time-intensive management: Maintaining and operating the platform can be time-consuming, particularly during initial adoption or complex deployments.
- On-prem maintenance challenges: Some users mention challenges related to on-prem maintenance and support responsiveness in certain scenarios.
How to Choose the Right AI-Driven Security Tools Cybersecurity Solutions for Your Organization
If you are evaluating AI cybersecurity solutions, start by matching tools to the layer of the security stack you need to strengthen. AppSec platforms help prevent vulnerabilities in software delivery, endpoint platforms focus on host-level detection and response, and AI-enhanced SIEM/SOAR tools improve investigation and automation inside the SOC. The best choice depends on where risk is growing fastest in your environment.
When selecting AI cybersecurity solutions, start by choosing the primary use case you need to improve most – AppSec, endpoint security, or SOC operations – then evaluate solutions on the criteria that matter for that domain.
- Prioritize IDE integration and real-time feedback: Look for tools that detect vulnerabilities as code is written. Native IDE integration ensures fast, in-context feedback without slowing development. This minimizes exposure and keeps security in flow.
- Look for pre-commit and post-commit remediation support: The best platforms prevent vulnerabilities before commits and fix them after scans. Dual-mode support helps reduce mean time to remediation across the SDLC.
- Ensure context-aware and safe fixes: Fixes should be accurate, explainable, and avoid regressions. Tools must consider code context and dependencies to apply safe, developer-aligned remediations.
- Choose scalable, policy-driven platforms: Select solutions that can support thousands of apps and users. Policy automation helps enforce controls across the pipeline while reducing alert fatigue.
- Demand visibility across the software supply chain: Good AppSec platforms offer unified insights from code to containers. Look for tools with real-time posture tracking, trend analysis, and SLA metrics.
- Optimize for developer productivity: Adoption improves when tools integrate easily and reduce time spent on security. Choose platforms that support fast fixes and minimize friction.
- Prepare for AI-driven code and threats: As attackers and developers both use AI, defenses must keep up. Select tools built to detect AI-generated code flaws and respond autonomously.
For organizations prioritizing developer-centric AI cybersecurity solutions with inner-loop IDE agents and outer-loop ASPM analytics, platforms like Checkmarx One stand out.
AI Cybersecurity Solutions FAQ
-
AI cybersecurity solutions use machine learning and automation to detect, prevent, and respond to cyber threats faster – often by learning patterns in telemetry and prioritizing the incidents that matter most.
-
No – high-performing organizations use AI to augment analysts and engineers: reducing noise, speeding triage, and suggesting next actions while keeping humans responsible for approvals and oversight.
-
Look for explainability (evidence for alerts), governance controls (policies/approvals), audit trails, secure data handling, and integration into workflows (IDE/CI/CD for AppSec, EDR/SIEM/SOAR for SOC).
-
They add context and validation – learning normal behavior, correlating signals across sources, and prioritizing alerts that show stronger evidence of exploitability or malicious intent.
-
Common categories include AI-powered application security, AI-powered endpoint protection, and AI-assisted SIEM/SOAR platforms for detection, investigation, and response automation.
-
Yes – AI-speed development increases risk, so strong solutions add guardrails in developer workflows and prioritize high-impact issues using context, validation, and governed remediation paths.
-
Prefer “governed automation”: clear policies, approvals for high-impact actions, explainable outputs, and measurable outcomes (noise reduction, MTTR reduction, and fewer recurring vulnerabilities).
Taking AI Cybersecurity to the Next Level with Checkmarx
For application security professionals navigating fast-moving development environments, Checkmarx One offers a unified platform purpose-built to meet the realities of modern AppSec. With full code-to-cloud visibility and deep integration into developer tools, it eliminates the need for context switching, allowing teams to detect, prioritize, and remediate vulnerabilities without slowing delivery. Real-time, in-IDE feedback powered by AI ensures security is embedded at the moment of code creation, while policy automation and posture management keep controls consistent across the SDLC.
What sets Checkmarx One apart is its ability to reduce alert noise and surface only the most critical, exploitable risks, helping teams focus where it matters most. Agentic AI drives platform-level automation and analytics contextual remediation at developer speed, cutting mean time to fix and minimizing friction between development and security. For organizations under pressure to secure software pipelines without compromising velocity,
Checkmarx delivers the operational scale, automation, and actionable insights needed to shift AppSec left, and keep pace with AI-driven development.