This document © Checkmarx, all rights reserved. Overview of the Last Week In AppSec It was an exciting week for Supply Chain Security: and we mean “exciting” in the “may you live in interesting times” kind of way. You almost certainly heard about the Axios compromise that led to remote access trojan installation, so we’re not going to discuss that further here. What you might not have heard of: Langflow code injection CVE from the prior week got added to the CISA KEV (Known Exploited Vulnerabilities) database just days after disclosure. Telnyx Python framework infected with malware, with a surprising abuse of .wav audio files to conceal malicious payloads. Langflow CVE-2026-33017 added to CISA KEV The popular low-code AI and RAG framework Langflow’s recent code injection vulnerability was added to the CISA KEV (Known Exploited Vulnerabilities) database this past week, demonstrating that this issue from earlier in the week is appetizing to adversaries. The core issue, as described in CVE-2026-33017, arises because attacker-controlled POST requests to /api/v1/build_public_tmp/{flow_id}/flow endpoints are passed directly to exec() without any sandboxing. Affected langflow services through (and including) 1.8.2 Fixed langflow versions 1.9.0 and newer Telnyx framework versions compromised The telnyx framework, a Python framework for handling carrier-grade voice and related functions, was compromised in a supply chain attack last week. Compromised versions (4.87.1 and 4.87.2) retrieved a spec-valid .wav audio file from a remote host (thus avoiding triggering suspicion), which had executable code hidden inside the audio frames. The payload varies, but harvests information from the infected computer and exfiltrates it via an HTTP POST to 83[.]142[.]209[.]203[:]8080/ Fortunately, the community identified and removed the affected versions quickly; but private registries and similar package proxies may retain the compromised revisions, so investigation and response is important. Checkmarx Malicious Package Identification data for affected versions of telnyx[ { "type": "pypi", "name": "telnyx", "status": "SCANNED", "version": "4.87.1", "ioc": [ "83.142.209.203" ], "risks": [ { "id": "097bc3bb508a0d30d69f8fa84fbf7541fd1d42e3", "description": "This package downloads a harmful file.\n### About\n\nUsing a dynamic analysis environment (also known as a Sandbox) we can monitor filesystem activity such as newly created files within the lifecycle of the code package.\n\nOnce new files are created, our technology analyzes each of the newly created files. In case a file is harmful, this risk is shown. \n\n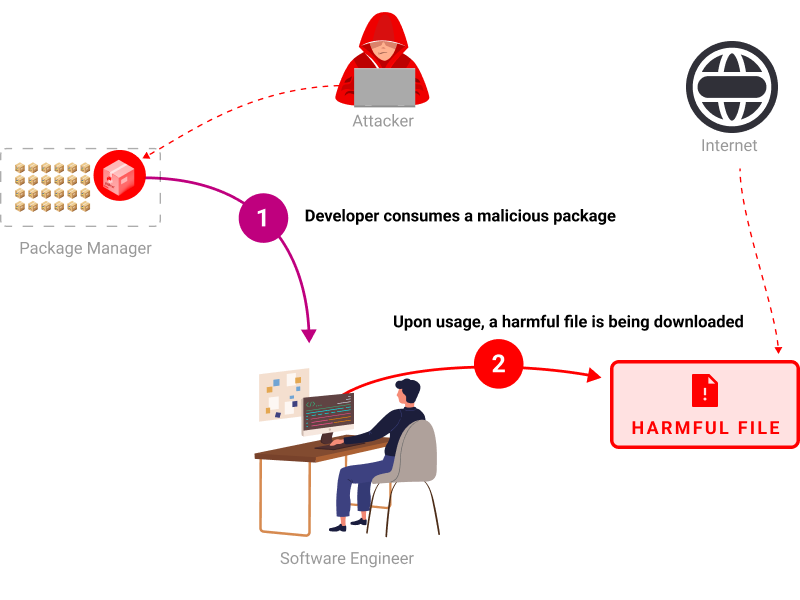", "title": "Harmful File Download", "score": 9 }, { "id": "53897b25c15efe005b722f26867307ef103445d5", "description": "This package exfiltrates computer and operating system information\n### About\n\nData exfiltration may be done in numerous ways such as through HTTP requests, DNS tunneling, various webhooks and more. It is common by attackers to try to exfiltrate sensitive information such as:\n- Credentials\n- Environment variables\n- SSH keys\n- Authentication tokens\n- Computer and operating system information\n- Network settings\n\n", "title": "Data Exfiltration", "score": 6 }, { "id": "d2994ee8b15325588d97ca045e8d88e369222f96", "description": "This package was manually inspected by a security researcher and flagged as malicious\n### About\n\nClassifying malicious packages is an internal process, analysis is done at scale automatically via multiple engines. Once there's a risk suspicion, this is forwarded to a security researcher for a manual evaluation.\n\nAttackers take advantage of the excessive trust in the open-source ecosystem and launch software supply chain attacks in the form of code packages. \n\nThe risk of having a package with a malicious payload is high. It's a common behavior for most of the malicious payloads to execute itself automatically upon installing or using the package. \n\n\n\nWhile some dependency vulnerabilities have the privilege to be kept as known issue due to risk-management, same does not apply in the case of a malicious package, and it should be removed with the highest priority.", "title": "Malicious Package", "score": 10 } ] }, { "type": "pypi", "name": "telnyx", "status": "SCANNED", "version": "4.87.2", "ioc": [ "83.142.209.203" ], "risks": [ { "id": "4241fa0d0251fb37cf5aa79b09177696a00d429c", "description": "This package exfiltrates computer and operating system information\n### About\n\nData exfiltration may be done in numerous ways such as through HTTP requests, DNS tunneling, various webhooks and more. It is common by attackers to try to exfiltrate sensitive information such as:\n- Credentials\n- Environment variables\n- SSH keys\n- Authentication tokens\n- Computer and operating system information\n- Network settings\n\n", "title": "Data Exfiltration", "score": 6 }, { "id": "43b4cfb9025057d57e99f5d4deeb3f01e5cc5b3e", "description": "This package was manually inspected by a security researcher and flagged as malicious\n### About\n\nClassifying malicious packages is an internal process, analysis is done at scale automatically via multiple engines. Once there's a risk suspicion, this is forwarded to a security researcher for a manual evaluation.\n\nAttackers take advantage of the excessive trust in the open-source ecosystem and launch software supply chain attacks in the form of code packages. \n\nThe risk of having a package with a malicious payload is high. It's a common behavior for most of the malicious payloads to execute itself automatically upon installing or using the package. \n\n\n\nWhile some dependency vulnerabilities have the privilege to be kept as known issue due to risk-management, same does not apply in the case of a malicious package, and it should be removed with the highest priority.", "title": "Malicious Package", "score": 10 }, { "id": "78aeaedb24de07ca9cdfd93d18d5ee0ad013a773", "description": "This package downloads a harmful file.\n### About\n\nUsing a dynamic analysis environment (also known as a Sandbox) we can monitor filesystem activity such as newly created files within the lifecycle of the code package.\n\nOnce new files are created, our technology analyzes each of the newly created files. In case a file is harmful, this risk is shown. \n\n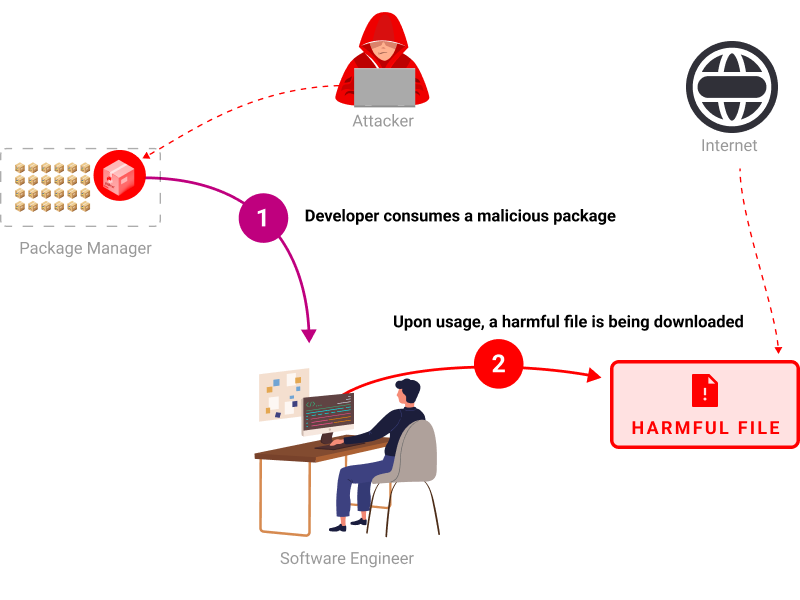", "title": "Harmful File Download", "score": 9 } ] } ] Researchers at JFrog have published a very nice technical analysis of the malware for those interested in the tactics in use. linkedin-app Share on LinkedIn Share on Bluesky Follow Checkmarx Zero: linkedin-app Tags: Arbitrary Code Execution Langflow Malicious Package Supply Chain Security Telnyx